How to install Qnap QTS OS on NVME M.2 SSD
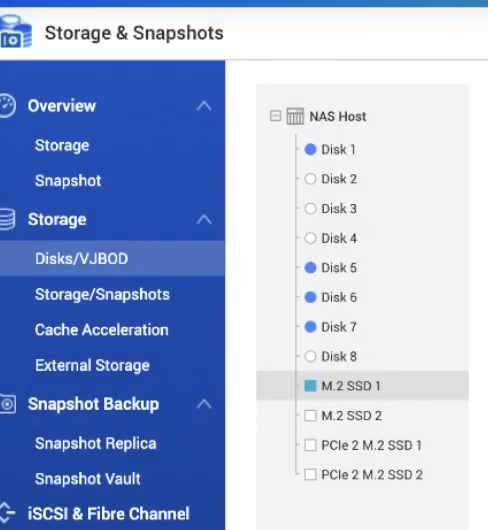
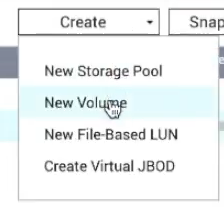
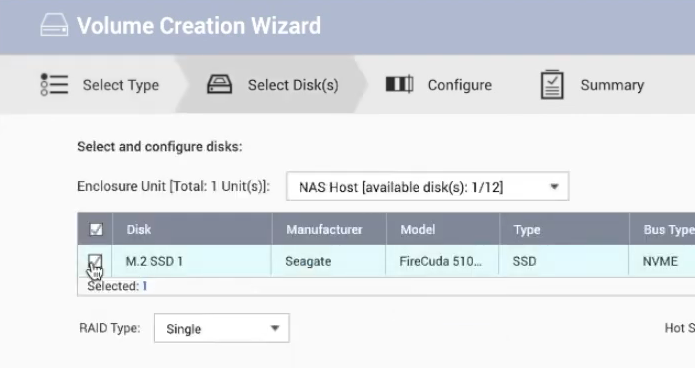
If you want to install OS on the NVMe, you should remove HDDs and keep only NVMe SSDs in there. The during the setup (will need to reset your NAS to factory defaults) you will be able to create volumes and RAID on a pair of NVMe M.2 SSDs (or 2.5inch SSDs). The system will then be installed on this volume.
Afterwards, you can put inside HDDs and build a RAID for these mechanical drives. Now all OS files will live on SSD also default app installation location will be NVMe. Alternatively, you can create NVMe volume and kee HDD RAID as the main storage location. All apps can be migrated to NVMe storage.
I hope this helps.
| Where to Buy a Product | |||
|
|
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
If you like this service, please consider supporting us.
We use affiliate links on the blog allowing NAScompares information and advice service to be free of charge to you. Anything you purchase on the day you click on our links will generate a small commission which is used to run the website. Here is a link for Amazon and B&H. You can also get me a ☕ Ko-fi or old school Paypal. Thanks! To find out more about how to support this advice service check HERE If you need to fix or configure a NAS, check Fiver Have you thought about helping others with your knowledge? Find Instructions Here
We use affiliate links on the blog allowing NAScompares information and advice service to be free of charge to you. Anything you purchase on the day you click on our links will generate a small commission which is used to run the website. Here is a link for Amazon and B&H. You can also get me a ☕ Ko-fi or old school Paypal. Thanks! To find out more about how to support this advice service check HERE If you need to fix or configure a NAS, check Fiver Have you thought about helping others with your knowledge? Find Instructions Here
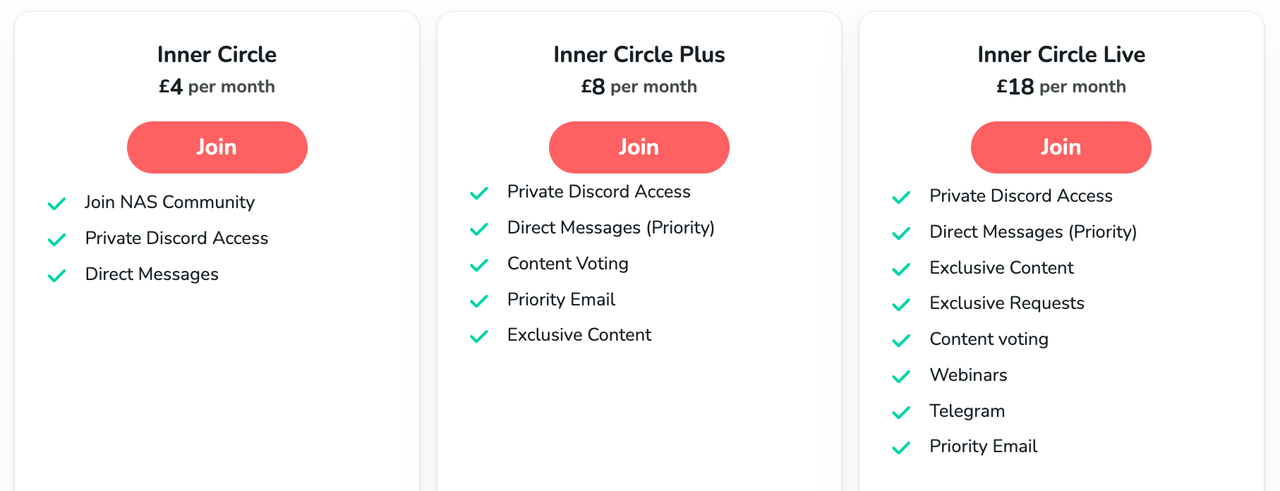
Private 🔒 Inner Circle content in last few days :
Terramaster F4 SSD NAS - Should You Buy? (Short Review)
Minisforum N5 Pro NAS Review - Did Minisforum just WIN at NAS?
What Can You ACTUALLY DO with HDMI on Your NAS?
Best NAS for under $499
Best NAS for Under $250 (2025)
Minisforum N5 Pro NAS - FIRST IMPRESSIONS
Access content via Patreon or KO-FI
Terramaster F4 SSD NAS - Should You Buy? (Short Review)
Minisforum N5 Pro NAS Review - Did Minisforum just WIN at NAS?
What Can You ACTUALLY DO with HDMI on Your NAS?
Best NAS for under $499
Best NAS for Under $250 (2025)
Minisforum N5 Pro NAS - FIRST IMPRESSIONS
Access content via Patreon or KO-FI



Fantastic video. Thank you very much.
REPLY ON YOUTUBE
Great video with lots of good info. I have had my TS-853 Pro for 9 years now and I have not had any malware. I keep it off of the internet and always keep updates applied.
REPLY ON YOUTUBE
This video needs an update and to go a bit more in depth
REPLY ON YOUTUBE
Lots of things to check. I have noticed in the new version of 5.1.5 QTS. The login options include 2 step verification (password and OTP/authenticator) or passwordless (1 step) – last option is username and authenticator. I am thinking the 2 steps seems safer.
REPLY ON YOUTUBE
i was going to buy a nas— im not now
REPLY ON YOUTUBE
If after installing Qnap QTS OS on NVME M.2 SSD’s I need to upsize the NVME’s, what would be the procedure? Will there be any dilemma when it comes time to migrate the OS to the larger drives (without losing access to data on the other drives). It would be cheaper to start with small capacity NVME but I’m reluctant until I know if that’s a bad choice or not.
I assume you have a RAID on those NVMe. Replace one NVMe at the time and allow it to rebuild. Otherwise start from scratch.
Please make an updated version of this video
REPLY ON YOUTUBE
This was a bit of a skimmy.
Overviews are one thing, but you did say you would show how to set this up securely. That wasn’t delivered here.
REPLY ON YOUTUBE
The more secure you make things, the harder it will be to manage and jump through to get what your after. You could use 2FA, and encrypt volumes, for single person or two, all of that really is not required.. as long as you have good passwords for each user., and just gets in the way anyway.
encrypted volumes also slow down you NAS as well, but depends on the CPU/RAM your NAS has. eg TS-451 would better than TS-251
I would prefer user-based folder access for security than 2FA just because 2FA and volume encryption works as a “whole” where as user password and permissions are “per-user”
Much more simple to manage. Many people may disagree, but its my NAS so… ???? Just make sure you use strong passwords and that’s it.. Also, its bad practice to keep changing passwords every 180 days,,
Companies used to do this in the past ,thinking it was more secure changing regularly, but all it REALLY did was ****** off employees.
Sorry, i manage my own security
REPLY ON YOUTUBE
not gonna lie I wasn’t thinking 20 minutes later all i’d hear is change password and scan for malware, that hardly keeps the NAS secure, if I had a good password to begin with my security isn’t increased by changing it constantly. and doing a malware scan isn’t keeping me secure, stopping malware get on my system would be. and being notified of the lack of security is moot and not keeping me secure. password, update and scan malware. that takes 20 seconds. I thought you were going to show us how to disable certain ports, etc.
REPLY ON YOUTUBE
Very BASIC security settings but the best security for QNAP is to keep all services OFFLINE completely so I absolutely NEVER use QNAP Cloud!
As of January 2023 QNAP still has major online security issues so I will not trust QNAP online servers, nor cloud services and especially not email notifications handled by QNAP.
For email notifications to be sent…QNAP needs QNAP email servers. Today QNAP products are still vectors for ransomware so please Do NOT connect to QNAP servers!
Novice QNAP users should be offline ONLY, therefore should not be using notifications nor QNAP Cloud.
REPLY ON YOUTUBE
Is myqnapcloud the only thing that “connects us to the internet.”
So my question is as long as I disconnect from myqnapcloud then a large majority of my risk goes away?
REPLY ON YOUTUBE
Can you do a video with the best firewall configuration for a multimedia qnap server like the tvs h674 without using the upnp method?…. thanks again.
REPLY ON YOUTUBE
I was hit by deadbolt ransomeware some weeks ago. Finally I got the key and my files have been fully decrypted. Thank you…
REPLY ON YOUTUBE
Have you done a video on how to set up let’s encrypt SSL for secure remote access to a NAS?
I’m just a simple Plex user and moved awhile ago, that whole time my Nas was unplugged and unused for 2 years and I recently plugged it back in after setting up a media room. My NAS wouldn’t update firmware so I updated it manually with a flashdrive and I needed to make a whole new mycloud account for some reason. It’s been a pain getting it all set up but it’s currently in sleep mode. Am I still safe?
I did manage to set up 2FA on admin and basic user account and I’ll see about setting up the X failed password revoking privileges
REPLY ON YOUTUBE
You didn’t mention running a VPN. 🙁 That saves so much complexity.
REPLY ON YOUTUBE
Worker with a reliable hacker is what I think is all over the world and I recommend a hacker parfait who works with good heart and sincerity Dee_hack11 is in Seoul☝️☝️☝️.
REPLY ON YOUTUBE
If i don’t have QNAP Cloud installed, does that mean that i am not connected to the internet?
Is sending email notification not a good idea, considering i don’t want to link my NAS to the internet?
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
.You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
.You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
Forgive that this may be a stupid question. But – if you have a QNAP NAS plugged in to your computer – and your computer is connected to the internet – does that mean your NAS is connected to the internet also? Or – is the hacking security risk purely for if you choose to directly connect the NAS to the internet (and therefore if you don’t, you risk free)?
REPLY ON YOUTUBE
will adding 2step verification change the way using share links work (ie: sending a share link to a shared folder on my nas to friends via email)?
REPLY ON YOUTUBE
Hi, Thanks for the great video!
Would you be able.to elaborate on sharing the file process to an external temporary user, please?
REPLY ON YOUTUBE
I miss the most important step, formatting and throwing away the QNAP.
REPLY ON YOUTUBE
Found the presentation very irritating. Why keep wizzing the cursor around the screen. Why not use a large black cursor. Don’t do everything so quickly.
REPLY ON YOUTUBE
I have an older TS-469 Pro running 4.3.4, so I guess my NAS is somewhat obsolete in terms of available applications such as Security Counselor
REPLY ON YOUTUBE
I don’t have the QuFirewall and the SSecurity Counselor available sadly, at least it just doesn’t want to install. Probably because my NAS is way too old, running QTS 4.2.6
REPLY ON YOUTUBE
WOW. Nice find here!! Great video.
REPLY ON YOUTUBE
Thank you. Wish I’d seen your recommendations BEFORE the Qlocker attack.
REPLY ON YOUTUBE
Hi, do you know if it’s really interesting for speed access to QTS ? Can you make a speedtest and give results ? And is it possible do this with HDD already used for RAID5 and QTS installed on them ? Thanks for answer !
hello sir your videos is so helpfull for me but i am confuse with how to configure alnet ssystem software with qnap nas storage i have configure qnap nas storage raid 6 with 4tb *12 hdd 1 hdd in spare but i am able to see live video but not able save nas storage so can you help me how to add path in qnap nas storage for save recording. Thanks,Jerry Upadhyay
REPLY ON YOUTUBE
If Norton or Bitdefender is installed as your main antivirus, will they be able to work on Qnap NAS? Instead of MacAfee, which for instance I don’t like.
REPLY ON YOUTUBE
Dude. Just a side note after watching 150+ videos. I have NEVER heard “noise in the background” so please stop apologizing for it. Not. Once. Ever.
REPLY ON YOUTUBE
I wish I saw this video before ???? apparently Qnap got hit with a massive ransomware attack this year and I had no idea. My files are all encrypted by some hacker asking for Bitcoin in exchange for passwords ????
REPLY ON YOUTUBE
Changing the default port does not enhance security. Security by obscurity. Port scanners can detect open ports it might fool some scripts.
Most people who serious about securing administrative interfaces dont expose them directly to the internet period.
Thats terrible terrible terrible security pratice.
A seperate vpn server with a dedicated vlan for admin is what you should be using to secure the admin interface and remotely managing the nas.
Example
Setup vlan 100 for management
Setup vlan 201 for cifs
Setup vlan 202 for iscsi
Setup vlan 300 for public network (internet)
Setup vpn server in dmz with one arm into the public network (300) another arm into vlan 100.
Setup logging and auditing.
Ensure 2fa exists for vpn service.
The qnap should have ports trunked with vlan 100,201,202 or dedicated ports.
Assign the services ip addresses in each of the ranges.
I never ever bother changing port numbers it simply offers very little security and may just elude some scripts scanning on certain ports
REPLY ON YOUTUBE