How do Asustor DeadBolt Ransomware works?
If you have EZ-connect turned on in your control panel, it seems to have crept in that way – also shows the danger of having your NAS accessible over public internet either directly or via reverse proxy, apparently …
apparently, this causes /usr/webman/portal/index.cgi to change to a version with malicious content and causes ADM to trigger a new update and the user presses for an update (or starts automatically if automatic update is enabled) and then the virus does its thing job (if you only encrypt a few kbytes at the beginning of each file, it is almost as bad as the whole file has been encrypted in most cases and therefore it can do enormous damage only after 15 minutes of activity) – and if you do reset / restart, the nose wants to do a reinitiation of the disks …
Now both QSNAP and ASUSTOR have been hacked – it’s only a matter of time before Synology and Netgear are also hacked – so keep your offline backups of your NAS up to date.
What can you do if you have been hit?
-you can pay Ransome and hope decryption will work (or use Emisoft)
-you can use PhotoRec or another app that restores freshly deletes files
-you can wait few years until someone creates a key or when computers become fast enough to decrypt AES-128
Regaining Access to the ADM Portal
If you are planning to continue using the existing drives you may regain access to the portal by running these commands below.
First open the Crontab tool to edit what files are being executed on the system.
crontab -e
You will notice a new line entry called cgi_install. Remove the line as found in this image
*/1 * * * * /bin/sh /usr/builtin/etc/cgi_install
https://forum.asustor.com/download/file.php?id=1544
Once that is done commit the changes. Then, remove the offending cgi_install file
rm /usr/builtin/etc/cgi_install
After that is done, navigate to the following to replace the bad cgi index file.
cd /usr/webman/portal
chattr -i index.cgi
rm index.cgi
cp index.cgi.bak index.cgi
This will restore the portal to it’s original state. Once inside the portal, turn off EZ-Connect to prevent future access to the NAS. Remember to block all remote access to the NAS from your firewall if possible.
Resources:
How to prevent this from happening again?
-Use Unifi firewall
-use routers with smart protection tools like DreamMachine
-never open any ports on the router unless it is for VPN connection
-keep NAS operating system on a separate volume / RAID
-back up
DeadBolt technical details [Qnap situation]
Threat actors will install the DeadBolt malware executable as a randomly named file in the /mnt/HDA_ROOT/ folder. Ransomware is initially launched with a config file, which likely contains various data, including an encryption key used to encrypt files.
The initial command to encrypt files is:
[random_file_name] -e [config] /shareThe /share folder is where QNAP NAS devices store user folders and files.
When encrypting files, the ransomware will only target files with the following file extensions:
.3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .ab4, .accdb, .accdc, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .ads, .agdl, .ait, .apj, .arw, .asf, .asm, .asp, .aspx, .asx, .avhd, .avi, .awg, .back, .backup, .backupdb, .bak, .bank, .bay, .bdb, .bgt, .bik, .bin, .bkf, .bkp, .blend, .bpw, .cdf, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cer, .cfg, .cfp, .cgm, .cib, .class, .cls, .cmt, .conf, .cpi, .cpp, .cr2, .craw, .crl, .crt, .crw, .csh, .csl, .csr, .csv, .dac, .dat, .db3, .db4, .db_journal, .dbc, .dbf, .dbx, .dc2, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .der, .des, .design, .dev, .dgc, .disk, .djvu, .dng, .doc, .docm, .docx, .dot, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .edb, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fhd, .fla, .flac, .flv, .fpx, .fxg, .gdb, .git, .gray, .grey, .gry, .hbk, .hdd, .hpp, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .iso, .jar, .java, .jpe, .jpeg, .jpg, .jrs, .kc2, .kdbx, .kdc, .key, .kpdx, .lua, .m4v, .mail, .max, .mdb, .mdbx, .mdc, .mdf, .mef, .mfw, .mkv, .mmw, .moneywell, .mos, .mov, .mp3, .mp4, .mpg, .mrw, .msi, .myd, .ndd, .nef, .nk2, .nop, .nrg, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nsh, .nsn, .nwb, .nx2, .nxl, .nyf, .obj, .oda, .odb, .odc, .odf, .odg, .odm, .odp, .ods, .odt, .oil, .orf, .ost, .otg, .oth, .otp, .ots, .ott, .ova, .ovf, .p12, .p7b, .p7c, .p7r, .pages, .pas, .pat, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .pem, .pfx, .php, .pio, .piz, .plc, .pmf, .png, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prf, .ps1, .psafe3, .psd, .pspimage, .pst, .ptx, .pvi, .pvk, .pyc, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qby, .r3d, .raf, .rar, .rat, .raw, .rdb, .rtf, .rw2, .rwl, .rwz, .s3db, .sas7bdat, .say, .sd0, .sda, .sdb, .sdf, .sl3, .sldm, .sldx, .spc, .sql, .sqlite, .sqlite3, .sqlitedb, .sr2, .srf, .srt, .srw, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stw, .stx, .svg, .swf, .sxc, .sxd, .sxg, .sxi, .sxm, .sxw, .tar, .tex, .tga, .thm, .tiff, .tlg, .txt, .vbk, .vbm, .vbox, .vcb, .vdi, .vfd, .vhd, .vhdx, .vmc, .vmdk, .vmem, .vmfx, .vmsd, .vmx, .vmxf, .vob, .vsd, .vsdx, .vsv, .wallet, .wav, .wb2, .wdb, .wmv, .wpd, .wps, .x11, .x3f, .xis, .xla, .xlam, .xlk, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xvd, .ycbcra, .yuv, .zip
Files are encrypted with AES128 encryption and will have the .deadbolt extension appended to file names.
DeadBolt will also replace the /home/httpd/index.html file with popup asking for a payment to get a key
If you pay, you get a key. The decryption key is located under the OP_RETURN output, as shown below.
When you enter this key into the ransom note screen, the web page will convert it into a SHA256 hash and compare it to the SHA256 hash of the victim’s decryption key and the SHA256 hash of the master decryption key.
If the decryption key matches either SHA256 hash, it will decrypt the files using the following command:
/mnt/HDA_ROOT/[encryptor_name] -d "[decryption_key]" /share
| Where to Buy a Product | |||
|
|
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
We use affiliate links on the blog allowing NAScompares information and advice service to be free of charge to you. Anything you purchase on the day you click on our links will generate a small commission which is used to run the website. Here is a link for Amazon and B&H. You can also get me a ☕ Ko-fi or old school Paypal. Thanks! To find out more about how to support this advice service check HERE If you need to fix or configure a NAS, check Fiver Have you thought about helping others with your knowledge? Find Instructions Here
ZimaOS is the BEST Beginner NAS OS - Watch Your Back UnRAID and TrueNAS !!!
30TB Hard Drives are TOO BIG ! (and here is why)
COMPLETE UGREEN NAS Setup Guide - 2025 EVERYTHING VERSION
$110 USB4 to 2x10Gb Adapter Review - What the WHAT?
UGREEN NAS Now has iSCSI, 2FA and Jellyfin (and more) - FINALLY!
Seagate 30TB Ironwolf and EXOS Hard Drive Review
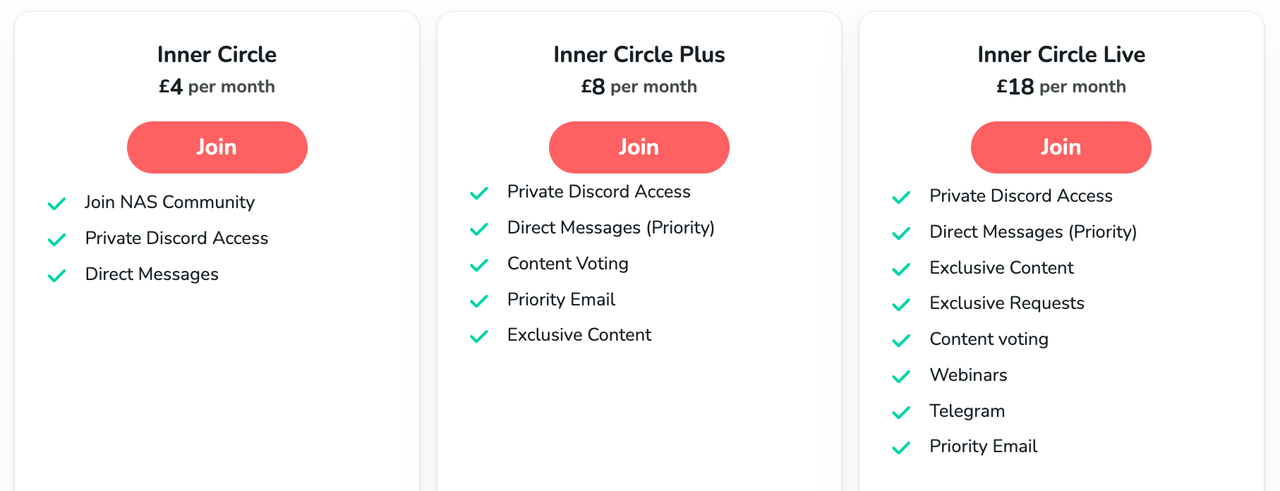
Access content via Patreon or KO-FI



User comments:
“I drive with an ASUSTOR (4-port) and does not seem to have spread from the boot volume to me.
I run with:
1 SSD as BOOT
3x HDD where everyone is NTFS MyArchive (likes to throw disks in the closet for cold storage), and those that were connected had not been encrypted.
Drove with everything off, firewall was set to whitelist instead of blacklist and it geoblocked everything that was not in the EU
SSH was turned off.
The only thing that was running was EZ-Connect.
Ran latest firmware (ADM), and no automatic update.”