WD My Book NAS Devices Being Remotely Formatted
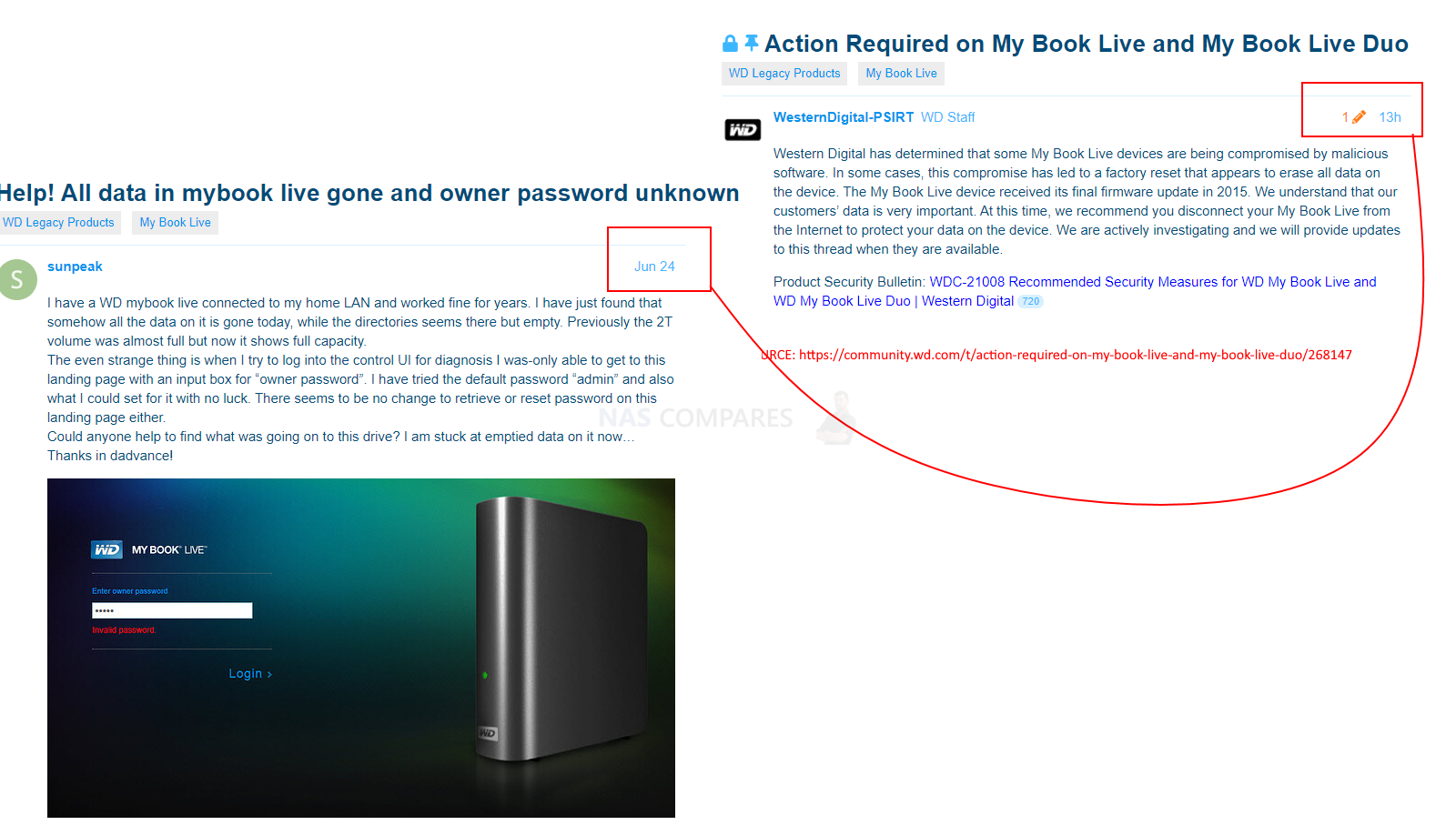
If you are reading this and you own a WD My Book or WD My Book Live Duo, then you might want to go check on it and maybe disconnect it from the internet for now. In the last 24+ hours, multiple users have reported that whilst trying to access their WD My Book NAS drive, they were barred entry with an ‘invalid password’ and mobile applications have ceased connectivity. Upon further investigation, they then find that their system has been completely formatted (ranging from directories, volumes and pools to in some cases everything) and all their data is now lost. This was originally raised over on the official WD Support blog here and not long after, multiple users at the same time have reported similar issues. Further examination of logs (once access to the system was possible) showed that remote access had been established to the system and a command to reset the system and storage be delivered. So what has happened? How did it happen and can the WD My Book Live data that people have lost be recovered?

How Did WD My Book Live NAS Drives Get Accessed Remotely
The WD My Book Live and My Book Live Duo are designed for access via the network and internet and were amoung some of WD’s first products for traditional NAS use, not just a HDD-on-the-internet, but have a GUI and dedicated CPU handling RAID, backups tasks and general system management. Remote access is conducted by accessing the NAS, through a firewall and via the official WD My Cloud Live servers (included with the cost of the device). However this remote access is what was used to push a command to the WD My Book Live system, executing the system reset with the following showing in the logs of the system )(from user Sunpeak on the WD Forums here)
Jun 23 15:14:05 MyBookLive factoryRestore.sh: begin script:
Jun 23 15:14:05 MyBookLive shutdown[24582]: shutting down for system reboot
Jun 23 16:02:26 MyBookLive S15mountDataVolume.sh: begin script: start
Jun 23 16:02:29 MyBookLive _: pkg: wd-nas
Jun 23 16:02:30 MyBookLive _: pkg: networking-general
Jun 23 16:02:30 MyBookLive _: pkg: apache-php-webdav
Jun 23 16:02:31 MyBookLive _: pkg: date-time
Jun 23 16:02:31 MyBookLive _: pkg: alerts
Jun 23 16:02:31 MyBookLive logger: hostname=MyBookLive
Jun 23 16:02:32 MyBookLive _: pkg: admin-rest-api
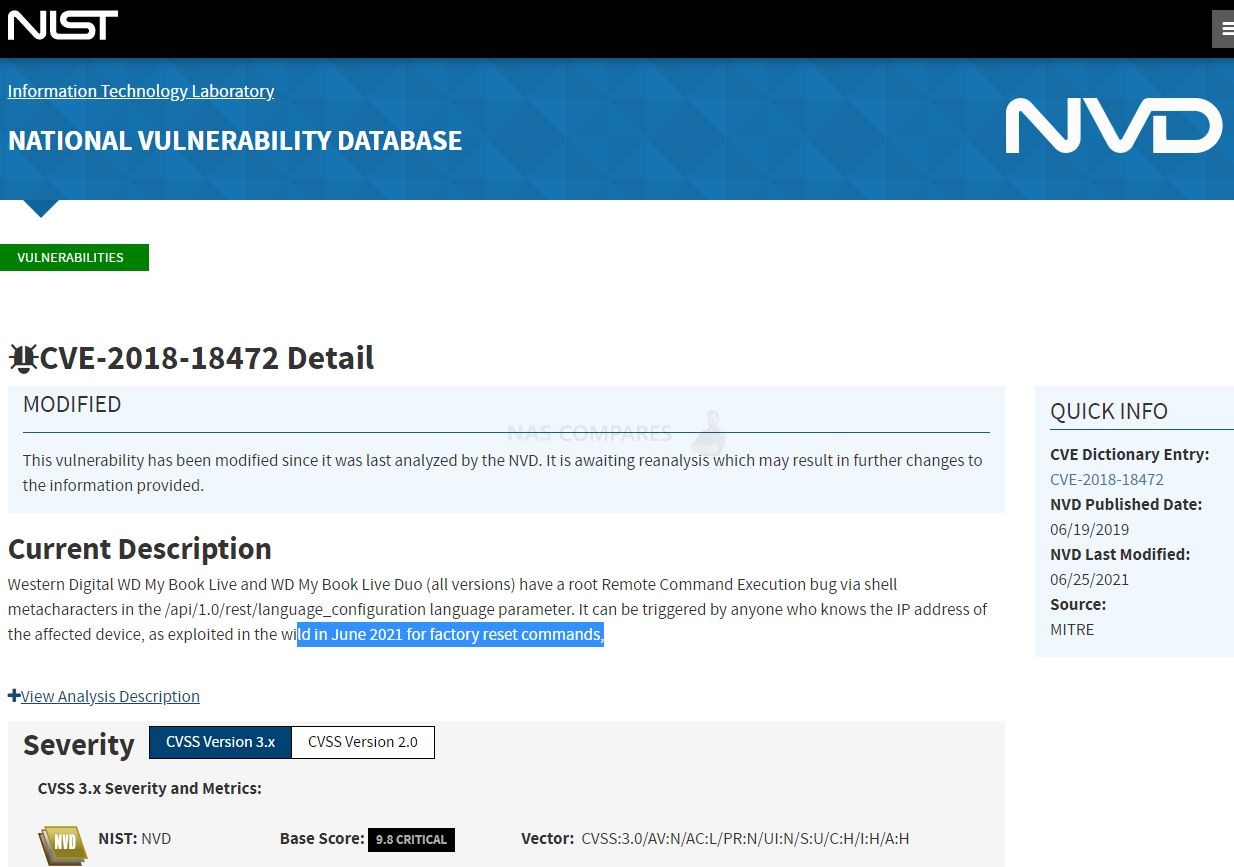
Since this was originally raised yesterday, lots of users have followed reporting the same, clearly showing this is an orchestrated attack of WD My Book Live systems, with the additional sad note that there has been no ransom.txt or other ransomware style communication left – meaning this has been done with the pure intention to destroy people’s data! Pretty lousy stuff! Since then this has gained considerably traction on multiple websites and the details on the National Vulnerability database (click below) has been updated serval times:
How Has Western Digital Responded to the WD My Book Live Attack
The response from WD on this NAS attack has been remarkably swift, considerably faster than I have personally seen from other brands suffering similar circumstances in previous years, with official instruction and widespread notification on their platforms in considerably less than a day. WD Have stated on their Security Advisory pages:
WDC Tracking Number: WDC-21008
Product Line: WD My Book Live and WD My Book Live Duo
Published: June 24, 2021Western Digital has determined that some My Book Live and My Book Live Duo devices are being compromised through exploitation of a remote command execution vulnerability. In some cases, this compromise has led to a factory reset that appears to erase all data on the device. The My Book Live and My Book Live Duo devices received its final firmware update in 2015. We understand that our customers’ data is very important. We are actively investigating the issue and will provide an updated advisory when we have more information.
Advisory Summary – At this time, we recommend you disconnect your My Book Live and My Book Live Duo from the Internet to protect your data on the device.
CVE Number:CVE-2018-18472
So, in short, WD believes this has been caused by the use of a remote command push to the WD My Book Live and WD My Book Duo Live NAS systems via an unpatched exploit on the system. They maintain that the issue is not caused from within their server-side, but are working on this right now to get to the bottom of it.
How Can A Vulnerability of the WD My Book Live Not Be Patching in a Firmware Update?
As previously mentioned, the WD My Book Live and My Book Live Duo were some of their earliest real NAS releases, as far back as 2010. Although these systems received numerous updates, the final update for this system was officially issued in 2015(see below)
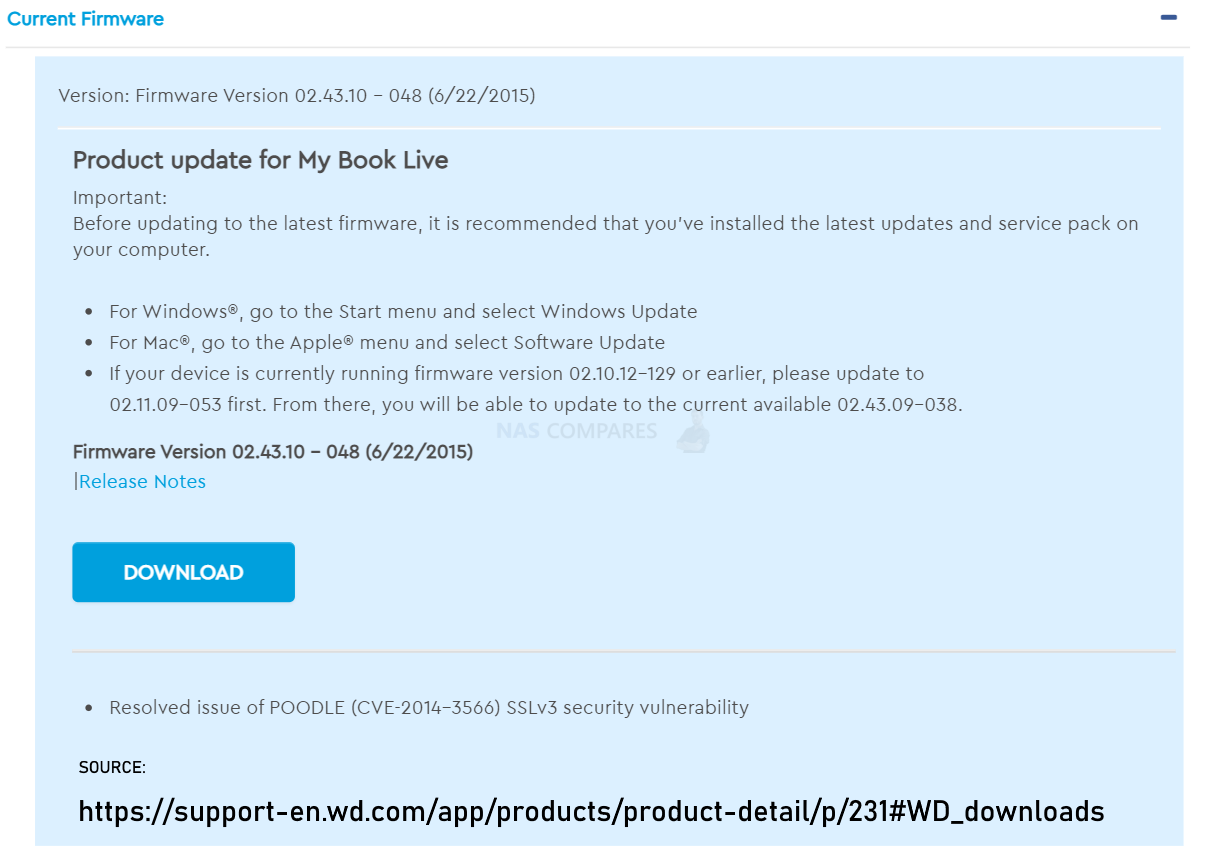
Given the predicted life of hard drives, the lifespan of products and their broader commitment to customers, it is not unheard of that they would cease firmware updates on a product line after a given period of time (the same can be said of the majority of software-enabled hardware in our homes and business environment). However, this comes as little comfort to those data that has been deleted. Additionally, this is a vulnerability that was raised back in 2018 by ‘Wizcase’ and found on numerous ‘first generation’ NAS systems that were released in this period. At that time, WD responded to this officially with:
“The vulnerability report CVE-2018-18472 affects My Book Live devices originally introduced to the market between 2010 and 2012. These products have been discontinued since 2014 and are no longer covered under our device software support lifecycle. We encourage users who wish to continue operating these legacy products to configure their firewall to prevent remote access to these devices, and to take measures to ensure that only trusted devices on the local network have access to the device.”
Once again, there is a balance here that users need to keep in mind between reliance on the hardware purchased and the rigidity of a solution a considerable length of time since release, as well as the maintenance of backups in a robust data storage strategy. It will be interesting to see how WD respond to this situation as it unfolds.
Can The Lost Data on the WD My Book Live and My Book Live Duo Be Recovered?
As this has been a format conducted on the system as a whole, it makes the recovery of data on a Factory Reset/Wipred WD My Book Live very difficult! In previous cases of malware encryption or malicious data destruction, many users have taken advantage of the tremendously useful PhotoRec tool (previously featured in the QNAP Qlocker Recovery guides). PhotoRec is a file data recovery software designed to recover lost files including video, documents and archives from hard disks (as well as legacy storage media like CD-ROMs) and memory cards. PhotoRec ignores the file system and goes after the underlying data, so it will still work even if your media’s file system has been severely damaged or reformatted. However, this is by no means full proof and does require a little more technical knowledge than many might have (with interfacing with the NAS in a software-accessible way being the first major hurdle). Here is an example of a PhotoRec recovery guide, but we are hoping quite soon for a more WD My Book Live specific guide with surface shortly.
Is My WD My Cloud or Regular WD My Book Direct Attach Storage Device Affected?
At this time there are no reports of this affecting the current generations of WD My Cloud, WD My Cloud Pro, WD My Cloud EX2 or WD My Cloud Sentinel Systems (which have far more recent firmware updates). Likewise, this will not affect WD My Book systems lack network/ethernet connectivity, as this lack both the means of communication and the software interface to inject the malicious command remotely.
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔
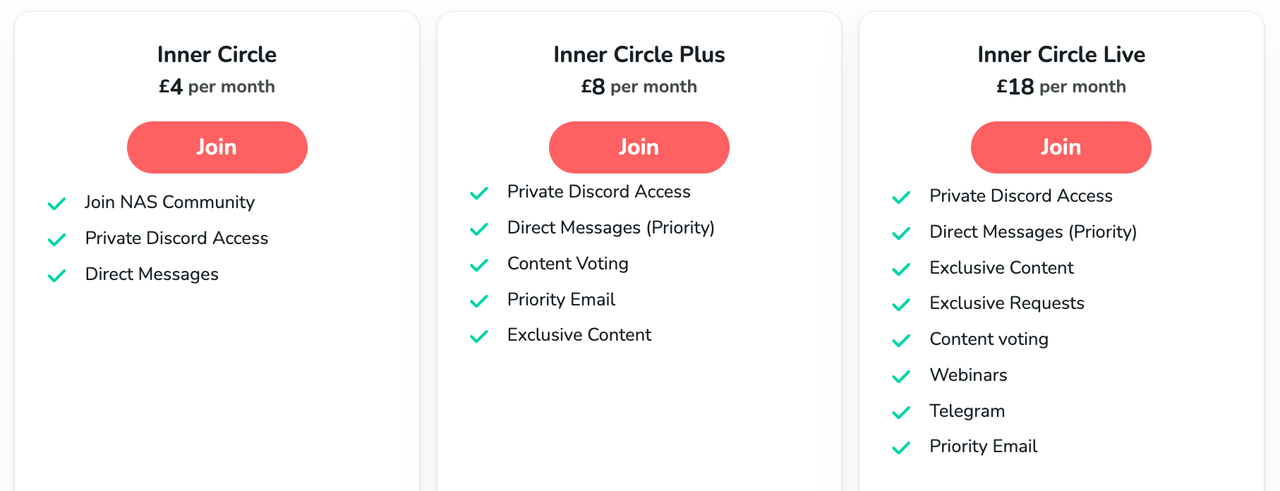
🔒 Join Inner Circle
Get an alert every time something gets added to this specific article!
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.

|
 |
Best NAS for under $499
Best NAS for Under $250 (2025)
Minisforum N5 Pro NAS - FIRST IMPRESSIONS
HexOS Q2 Update - What's Changed?
5 Exciting NAS Coming Later in 2025
Beelink ME Mini vs GMKtec G9 vs CWWK P6 NAS Comparison
Access content via Patreon or KO-FI



The hackers are probably from Apple iCloud. Annoying subscription based program from Apple that keeps popping up on my Mac and iPhone, im pretty curious to think they have something to do with that mybook attack, till this day I still store data on mybook but never connected it online, because I always been WOKE!
REPLY ON YOUTUBE
Shut T F Up! Nothing said!
REPLY ON YOUTUBE
Is it safe to keep using WD My Cloud if I turn off remote access in the menus? Or should I block access in the rougher? It’s just I find the WD my cloud useful for streaming Films and TV shows to TV. Also, it being a network drive it’s always on so don’t need to turn on PC for a network share. I did use to use it for backing up photos, off my phone, but don’t trust it with my personal files. So just use it for just media.
REPLY ON YOUTUBE
i have 2 of the my book live drive. none where wiped but i unpluged the bothe from being online. and i got my cupon for a new one at 40 percent discount , just waiting for my new device 😀 8 tb ex2 ultra .
REPLY ON YOUTUBE
i have a my book live duo 8tb it has a usb on it, can i just simple plug it into my pc usb, without router, to put more stuff on it, use it as a external drive, any info be appreciated
REPLY ON YOUTUBE
Has there been a fix?
REPLY ON YOUTUBE
An attempt to kill off the old WD systems so it could be anybody.
REPLY ON YOUTUBE
But this doesn’t have any influence on the QNAP Nas?
REPLY ON YOUTUBE
I am also one of the affected users, I disagree that WD acted quickly as it was 2 days after I reported the issue I got the general disconnect email. I only had 1.2tb in use on a 4tb my book live duo but it now reports 3tb in use. Waiting for WD to say how to proceed, hopefully they will offer some sort of data recovery service, I bought mine new from PC World in 2016 so I guess it was old stock, but even so for a network connected device WD should be updating security regularly.
REPLY ON YOUTUBE
If you have VPN this can be prevented.
REPLY ON YOUTUBE