QNAP Issue a Public Statement About the QLocker Ransomware Attack on Thousands of NAS Devices
It has been a rather turbulent few weeks for QNAP NAS users (and indeed the brand itself) since the initial impact of the QLocker ransomware impacted the storage systems of thousands of users. With many users waking up to find their data (in large parts) inaccessibly encrypted, seeking resolution with QNAP in effects to avoid paying the culprits $500+, this has been a rather troubling time for the brand, as well as the NAS Server industry as a whole. We have covered the development of QLocker over on YouTube, as well as shared potential resolutions with some absolute heroes over on Reddit, but QNAP has now issued an official statement on this, which we have replicated below.
The original statement can be found on the official QNAP page here
https://www.qnap.com/static/landing/2021/qlocker/response/en
QNAP Statement About Qlocker Ransomware
Recently the Qlocker ransomware launched a hostile campaign against QNAP NAS and has caused inconvenience and data loss for our valued users. We understand that our users are deeply troubled by this incident. While it has always been QNAP’s top priority to timely patch software issues and to release relevant information, we stand behind our commitment and are doubling our efforts to the continuing enhancement of the security features provided in our products. We sincerely invite our users to join us and work together toward the goal of fighting against ransomware, in order to make the Internet a safer place for everyone.
Incident Description
On April 16, 2021, we released an updated version (16.0.0415) of the Hybrid Backup Sync (HBS) app to add new features and to address certain security issues described in the QNAP Security Advisory QSA-21-13. On April 21, we began to receive user reports about possible ransomware attacks. Subsequently, after our initial investigation, it is confirmed that the Qlocker ransomware is exploiting one of the patched HBS vulnerabilities against unpatched QNAP NAS that are directly connected to the Internet.
The attacker took advantage of a patched HBS vulnerability. Once the weakness is exploited, the malware could obtain the inappropriate permission level of the QNAP NAS involved. After the NAS is breached, the attacker would insert malicious code into the system to delete all snapshots and to compress user files with a password by using the built-in 7-Zip utility that is intended for normal file compression/decompression operations. After the encryption begins, Qlocker will leave a ransom note and delete itself to increase the difficulty of our investigation.
Based on the limited information we’ve gathered from early-reported cases, we released updated detection rules of the QNAP NAS Malware Remover app to detect and stop malware activities. We’ve also added short scripts to attempt extractions of the encryption key when the compression is still in progress.
Subsequently, on April 22, we released a piece of Product Security News to urge our users to install all recently-released updates before we can confirm the actual attack path. And after the path is identified, we updated the Malware Remover rule again to quarantine the HBS code in question for unpatched QNAP NAS.
Symptoms
- Infected but not yet active
- No abnormality will be observed for Qlocker-infected QNAP NAS.
- Active (encryption in progress)
- If Qlocker is currently active (encryption/compression in progress), the filename extension of user files will become “.7z” one after one. Alternatively, in Resource Monitor, the 7z process is occupying an abnormally high level of system resources.
- Post-activity (encryption ended)
- After Qlocker ended its malicious activity (encryption/compression ended), the filename extension of all user files (size < 20MB) is now “.7z”. A ransom note (clear text file) is also generated on QNAP NAS.
Timeline of Our Response to Qlocker
- March 19, 2021
- Received HBS security issue report.
- April 16, 2021
- Released the patched HBS app for the current version. To protect users who have not yet applied the update from attacks, we adjusted the disclosure time for the corresponding security advisory.
- April 21, 2021
- Began to receive user reports about ransomware attacks. We immediately initiated our investigation.
- April 22, 2021
- Updated the Malware Remover detection rule to stop the Qlocker encryption/compression. We’ve also released Product Security News and the corresponding security advisory on the same day.
- April 23 to 25, 2021
- The QNAP technical support staff around the globe worked around the clock with affected users to test and purge Qlocker, and to offer our help by all possible means.
- April 26, 2021
- Added new Malware Remover detection rule for Qlocker to quarantine the HBS code in question for unpatched QNAP NAS.
What a Malware Remover scan does
- By running a Malware Remover scan on a QNAP NAS with Qlocker infected (not yet active), the Qlocker malicious code will be purged. If an unpatched version of HBS is detected as well, the HBS code in question will be removed.
- By running a Malware Remover scan on a QNAP NAS with Qlocker active (encryption/compression in progress), the encryption/compression will stop. The scan will also attempt to extract the encryption key used for the attack. If an unpatched version of HBS is detected as well, the HBS code in question will be removed.
- By running a Malware Remover scan on a QNAP NAS after the Qlocker attack (encryption/compression ended), the HBS code in question will be removed if an unpatched version of HBS is detected.
For all Malware Remover activities, corresponding system event log will be generated.
User-actionable items against Qlocker
For all users, we strongly recommend running a manual Malware Remover scan while the QNAP NAS is connected to the Internet. Malware Remover will update its detection rule to the latest version, and then detect if your QNAP NAS is under the influence of the Qlocker ransomware and the patched HBS weakness.
However please be advised that the way your QNAP NAS is connected to the Internet also affects the overall system security. To proceed securely, please refer to the general recommendations listed in the next section.
Additionally,
- Encryption/compression active or ended
- If your QNAP NAS is under the influence of Qlocker, regardless of the encryption/compression status, do not shutdown or reboot the NAS. Do not update the NAS OS as well. Please run the above mentioned manual Malware Remover scan and contact QNAP technical support right away. We will inspect your QNAP NAS to determine if your files could be retrieved;
- Infected but not yet active
- If Malware Remover detects Qlocker and purges it from your QNAP NAS, and your files are intact, please take the measures listed in the general recommendations at your earliest convenience to enhance NAS security;
- Unaffected
- If Malware Remover did not detect Qlocker in your QNAP NAS, you should still take the measures listed in the general recommendations at your earliest convenience to enhance NAS security.
General Recommendations
We strongly urge that users do not directly connect their QNAP NAS to the Internet. This is to enhance the security of your QNAP NAS. We recommend users to enable the VPN server service on their router. To access your QNAP NAS from the Internet, first establish a VPN connection to your router, and then connect to the QNAP NAS via VPN. This can effectively harden the NAS and decrease the chance of being attacked. You can also use the myQNAPcloud Link relay feature provided by QNAP. For details, please refer to the QNAP Blog article: https://blog.qnap.com/nas-internet-connect-en/
While we are actively extending our investigation to a broader scope, there is a series of actions that our users can take to make their QNAP NAS more secure for defending against cyber attacks. These actions include:
- Enable auto update settings, or periodically check for OS and app updates manually
- Refer to the 3-2-1 backup strategy and back up files stored in QNAP NAS
- Please note: if you store the only copy of your files in QNAP NAS, even if you’ve enabled data protection features such as RAID and snapshots, your data is not protected against all possible risks. RAID only protects against disk failures, and snapshots offer protections for the scenario of ransomware attacks from your personal computer. To make sure your files are safe and sound, back up your NAS data, or back up the backup file stored in your QNAP NAS.
- Please refer to the second half of this QNAP Blog article for recommendations on security settings to increase NAS security: https://blog.qnap.com/nas-internet-connect-en/
- Sign up a QNAP ID and subscribe to our security advisories to receive our latest security update information: https://account.qnap.com/
Acknowledgement
We would take this opportunity to acknowledge the contribution of ZUSO, the Taiwan-based information security company, for reporting the issue and helping with the response of the incident. We will continue working with ZUSO and other security research companies/teams to enhance the security and protection of all QNAP products.
So, What Do You Guys Think?
Now QNAP has issued a formal statement on this, I would genuinely love to hear your thoughts on this – Share your thoughts below in the comments below, contacting us (if you are affected) on the free advice section or over on YouTube. I look forward to sharing your thoughts, reactions and feedback on QNAP’s official statement later this week on YouTube, so if you can keep it constructive and relative, that is always the best way forward! Thanks for reading and I look forward to hearing from you!
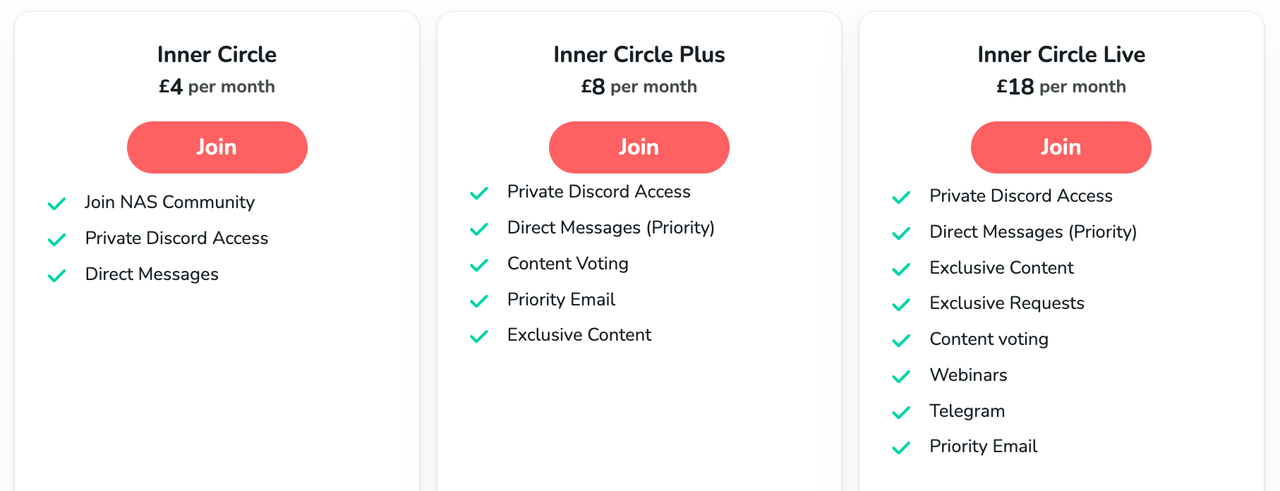
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔🔒 Join Inner Circle
Get an alert every time something gets added to this specific article!
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.

|
 |
Minisforum N5 Pro vs Aoostar WTR Max - The BIG Showdown
Do MORE with Your M.2 Slots - GREAT M.2 Adapters!
5 Top Tips for Content Creators Buying a NAS
Terramaster F4 SSD NAS - Should You Buy? (Short Review)
Minisforum N5 Pro NAS Review - Did Minisforum just WIN at NAS?
What Can You ACTUALLY DO with HDMI on Your NAS?
Access content via Patreon or KO-FI





Hello sir .. recently (3 weeks ago) I brought home the QNAP TS-673A NAS. It is my first. I am a musician, looking for a less complicated, faster data throughput option mainly to avoid the audio sample libraries’ often AGONIZINGLY slow loading times. (The ‘less-complicated’ meaning that, I don’t want a setup like my current – every USB port on my laptop taken, including the Thunderbolt4 port acting as a “super-fast 3.1 Gen2 interface” to a StarTech Gen2 hub, with 4 short Gen2 cables out to portable WD Gen2 drives…) YES, it’s a nightmarish mess, but gets me the speed I want. But when I update the Kontakt library database for example, I need to scan 5 folders on 5 separate drives – instead of just 1, which I hope to achieve, and with similar speed, in my new QNAP setup.
This would be up and running a few weeks ago, but I am busy touring with the band I play with this summer and seldom home on weekends. But in my research about QNAP NAS’s (including, thankfully, many of your fine contributions here on YT) .. it didn’t take long at all to learn of the security exploits and dreaded RW attacks. So my ‘rush’ to setup this NAS – turned into something not so rushed at all. One alternative, according to a review of my same product on Amazon, indicates the fellow used something called “TrueNAS Scale” – a freeware, open-source OS he claims to be much more secure than what QNAP offers, but what others say is incredibly complex and non-user-friendly.
So right now, I sit on a day off with the NAS plugged in (not powered on) populated with 1 WD “Gold” Enterprise 8 TB drive, along with 4 WD “Red Plus” NAS 8 TB drives, ready for a RAID 5 configuration. My laptop’s Thunderbolt 4 port is connected to one of the NAS’s USB faster ports (not the slower USB-C which you rightfully ridiculed in your TS-873A review). The ‘Power’ button has not been pushed yet. I have a network connection ready for a cloud install when I finally turn it on, and I have your 2022 QNAP NAS Setup Guide series of 6? videos all cued up and ready to follow with precision. So I guess my only question is: IS IT SAFE, on this day, TO DO THE STANDARD QNAP QuTS “hero” install??? Or should I try the alternative TrueNAS Scale install, for which there are a few walkthrough videos I could follow as well? I’m leaning toward QNAP … but only if it is safe. Answers from anyone well-experienced NAS’ers are welcome too. Thanks you sir, and keep up the great work you do!
REPLY ON YOUTUBE
The best person to contact is #GLOCYBER ON INSTAGRAM he got all the ideas on each of the virus extension. He was able to repair mine.
REPLY ON YOUTUBE
It has been a week when I got infected but today I saw a comment that recommended me to #GLOCYBER ON INSTAGRAM and he was able to open all my files.
REPLY ON YOUTUBE
My MacBook was affected and I had no option than to contact #GLOCYBER on instagram. He did helped me recover all my files.
REPLY ON YOUTUBE
I suggest you should all contact #GLOCYBER ON INSTAGRAM. He was able to help me fix my computer.
REPLY ON YOUTUBE
My company system was infected too. We all couldn’t use our computers because it spreads to everyone computer. Our manager has explained that he hire #GLOCYBER ON INSTAGRAM and he was able to fix it. At least, we could have our jobs again.
REPLY ON YOUTUBE
My mums computer was infected and she asked me to help her. Although I don’t know how to fix it so I contacted #GLOCYBER ON INSTAGRAM and he helped us. He charged us a bit but it was very affordable. Thanks to him.
REPLY ON YOUTUBE
I got infected too. It was annoying seeing your computer but can’t use it. I did asked my technician and he suggest I should contact #GLOCYBER ON INSTAGRAM. I did contact him and he was able to help me out.
REPLY ON YOUTUBE
Am a photographer and it affected all my clients files and pictures. It affects my animal documentation pics. I almost cried, then I make my research and found out that #GLOCYBER ON INSTAGRAM has been helping out. He did mine and thanks to him.
REPLY ON YOUTUBE
Thanks to #GLOCYBER ON INSTAGRAM. He was able to fix my computer and all my files are normal.
REPLY ON YOUTUBE
My NAS was attacked by the virus but I was able to reach out to #GLOCYBER on INSTAGRAM and he could figure it out.
REPLY ON YOUTUBE
I got affected by the division of the virus. And I could not read for my exam because it encrypted all my lectures note. Thanks to my lecturer who recommended #GLOCYBER ON INSTAGRAM to help me recover my files. He did and am so happy.
REPLY ON YOUTUBE
Am a student too and it lock all my pdf and everything other thing in my laptop. Am so happy I got help from #GLOCYBER ON INSTAGRAM. He did a marvelous work and now I have all my files back.
REPLY ON YOUTUBE
I recommend you all to contact #GLOCYBER ON INSTAGRAM. He was able to help me recover all my encrypted files. Am glad I met him earlier.
REPLY ON YOUTUBE
I was dead in need of my computer. But I could not all because of this virus. I was recommended to #GLOCYBER on instagram and he responded to me and helped me fix my laptop.
REPLY ON YOUTUBE
Am able to contact #GLOCYBER on INSTAGRAM and I showed him what has happened to my computer. He was able to assist and get my computer free from the virus.
REPLY ON YOUTUBE
I was affected too and I talked to #GLOCYBER ON INSTAGRAM . he could help and he did recover all my files and photo.
REPLY ON YOUTUBE
It was through the help of #GLOCYBER on instagram that we ware able to get our money photos decrypt. The virus has held all the pics in the system.
REPLY ON YOUTUBE
It was #GLOCYBER on instagram that was able to help me fix all my files and get them decrypt. He really did a great work and am happy I met him.
REPLY ON YOUTUBE
I found a legit cyber professional. He is #GLOCYBER on instagram. he was able to help me fix and decrypt all my encrypted files. Thanks to him for his kindness.
REPLY ON YOUTUBE
Contacting #GLOCYBER on instagram was the best thing I did after my files got infected. He quickly decrypt all my files and get me free from the virus.
REPLY ON YOUTUBE
This virus has been attached to my files for more than a week. It was my dad who directed me to #GLOCYBER on instagram and he was able to get rid of the virus. Thanks to him.
REPLY ON YOUTUBE
my files have been encrypted and I thought I would never use them again. My lecturer told me to reach #GLOCYBER on instagram and he was able to help me recover my files from the virus. Thanks to him.
REPLY ON YOUTUBE
Contacting #GLOCYBER on instagram was the best thing I did after my files got infected. He quickly decrypt all my files and get me free from the virus.
REPLY ON YOUTUBE
Am happy I could contact #GLOCYBER on instagram and he was able to help me remove all the virus. My exams files are free now.
REPLY ON YOUTUBE
My computer was affected too and it got stuck of all the virus. Thanks to my sister who had recommended #GLOCYBER on instagram. I search him on google and he responded to me. Thanks to him.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
…You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
…You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
????I was so glad when I finally realized and get in touch with Glo Cyber while I used the contact above. He is indeed a genius and his skill are authentic. I rec. everyone to appreciate his efforts.
REPLY ON YOUTUBE
People keep talking about Scott. I think he is good. I will try him.
REPLY ON YOUTUBE
Someone recommended you ????and you also helped me recover mine too. You a genius indeed
REPLY ON YOUTUBE
Someone recommended you ????and you also helped me recover mine too. You a genius indeed
REPLY ON YOUTUBE
You’re ???? such a genius, I really appreciate your services, fast and safe recovery process.
REPLY ON YOUTUBE
Just come here because my NAS has been compromised! I’m so annoyed and this has been a major blow for my business (video production company).
REPLY ON YOUTUBE
People should know about this this is madness, just happenned to me? 8 months later?? Could they have warned their F*ing customers??!!
REPLY ON YOUTUBE
i was infectet now on 7 dec 21
REPLY ON YOUTUBE
I don’t use my over the cloud I only use it with my local network. Is it safe that way ?
REPLY ON YOUTUBE
The little graphics was very helpful. I learned my lesson for sure on what having a backup actually means.
I naively bought my NAS thinking it would be my own little personal cloud machine and sole backup (thinking raid would keep me safe forever) for my documents, photos, and videos.
Now I realize I’m going to still have to spend more money on cloud services and be very careful with my qnap nas.
I was immediately thinking of switching to Synology since you said it’s more user friendly and all I really use my NAS for is backup and as a cloud drive to put my files into it and be able to retrieve them on my phone. Unfortunately, from what I’ve seen on the appstore the other Nas company apps look like they are just as rough, slow, and confusing to use as Qnap’s (Qmanager and Qfile). I don’t understand how “downloads” and “Qsync” works on Qfile for example so I’ve been just moving files manually as I would on any other cloud app.
For now I’m staying with my TS-453D.
But still have mixed feelings about it.
REPLY ON YOUTUBE
So I got stung by the Qlocker ransom ware attack and apparently it was caused by a back door issue relating one of the apps, hybrid desk station? I can’t recall I was too busy fuming at how a company could have this vulnerability. And I do appreciate the support the qnap staff have tried to give in recovering the files and data, but when the process broke down and they let communication fade, with lack of support to get a resolution I soon lost patients with them and decided to let go of some files. I thankfully did have back ups but when your sync does the backing up it basically just had a knock on effect so ran some files where synced to pc, and a back up hard drive before I had noticed. Thankfully larger files where left and they only went after the smaller file sizes.
Anyway long story short, always back up your data manually on an off line hard drive. This is the only real way you can secure a true back up of your files. Thankfully an old NAS gave that option to me.
REPLY ON YOUTUBE