Possible Recovery Method for QLocker Encryption On Your QNAP NAS
As many of you may be aware, a number of QNAP NAS devices have been struck in the last week+ with a ransomware attack, dubbed QLocker. It appears the root method of this intrusion was through one of two command injection methods, made via vulnerabilities in the QNAP HBS and Multimedia Console and Media Streaming services add-on, which instructed the system to begin archiving smaller files into 7z (.7zip) archives, with a withheld key. Then a readme.txt file would be left with instructions of making a payment to the hackers in exchange for the password to extract your files. Since this attack has taken place, there have been several methods that have appeared on forums, Reddit, YouTube that offer potential solutions to this (without resorting to paying the hackers) with each having a varying degree of success based on the extent to which your QNAP NAS ha been hit. In the next week or so, I am contacting many of these users who have managed to find/create methods of QLocker file recovery, in efforts to share them here and get them seen by as many people as possible. The following guide was provided (and full credit to him!) by Reddit user Open_Bumhole and though he does highlight that this is based on the further guides provided over on BleepingComputer, he has handily created a more user-friendy version of the instructions in order to help those that might have been affected.
Below is a video detailing how to strengthen your NAS security. Though you can scroll right past if you like to see the guide provided by Reddit user Open_Bumhole to use TestDisk to recover your Encrypted Files.
The Full Reddit thread by Open_Bumhole can be found HERE and also has links to further useful resources to help others out if they are still without access to their data. It is worth remembering though that the following steps, although presented in a much more chewable fashion, this is still covering a process that most would consider highly technical. This method (and indeed any method that requires SSH and more invasive command lines) do have the potential to make things worse if followed poorly, so you should not attempt the following unless you know what you are doing and/or at a loss for any other option.
Using TestDisk to Attempt to Recover Qlocker Encrypted Files
Open_Bumhole: Haven’t seen this posted yet and it might really help if you don’t have recent backups or whatever. It’s inconvenient and will require a lot of manual organising once the files are recovered, but it’s working for me. The crux is that your unencrypted files are marked for deletion and may be recoverable if you act soon. This works even if you have restarted your nas since the attack
In the event these steps are difficult to follow, I’ve reworded them keeping the steps numbered the same. If it’s still difficult in places let me know and I’ll try to edit or clarify:
This fix works by recovering files that are marked as ‘deleted’ by the filesystem but are not yet overwritten by other files (the data is still there, just inaccessible / free to be overwritten)
Pre-requisites:
-
Try not to do anything that will write files to your NAS drive after the attack! The more data you modify, the more likely your NAS OS will overwrite some ‘deleted’ data.
-
Secure your NAS before beginning. The bare minimum is to make sure you have updated your NAS firmware, official apps, and malware remover, and ensure that the malware remover has deleted the ransomware. A next best step would be to disable UPnP in your router and to disable any QNAP apps you do not use on your NAS (HybridBackupSync, Multimedia Console, etc) and maybe make it completely inaccessible from the internet in general to prevent reoccurrence.
-
Enable SSH connections on your NAS if not already enabled and do not expose the port here to the internet (Control Panel -> Network & File Services -> Telnet/SSH -> Allow SSH Connection)
-
If you’re on windows, get an SSH client like PuTTY.
If you are uncomfortable navigating an ssh terminal, two useful commands are pwd which will show you the current directory that you are inside (e.g. /mnt/rescue-share) and ls which will list all files and directories in your current directory.
-
Create a share drive on your computer. This will be used to store the recovered files so make sure you have enough space, instructions for Windows are here.
For the next steps, let’s assume the new share is accessible at \\MY-PC\qfix and my windows username is Tulip
Note that you might struggle to connect to this from the NAS if you don’t have a password on your computer account, so set one up temporarily. I think you can also bypass the share and just use plug an external drive into the NAS if you like/that’s easier but note that if the ransomware is active, this will get encrypted too!
2. Connect to your NAS via ssh. Host: {nas admin account name}@{nas address} e.g. admin@192.168.0.60. Port should be 22 or whatever you configured in control panel. Password is the NAS account password.
3. You’ll see a text-based menu titled “Console Management – Main menu”. Press Q to select Q: Quit (return to normal shell environment) and hit enter. Confirm this with Y and enter. You’ll now be at a raw ssh prompt looking like [~] # where you can enter commands.
4. Mount the shared drive from your PC onto your NAS so you can access it with these three commands:
mkdir /mnt/rescue-share
sudo mount -t cifs -o user=<USERNAMEOFREMOTECOMPUTER> //XXX.XXX.XXX.XXX/<NAMEOFYOURSHARE> /mnt/rescue-share
cd /mnt/rescue-share
Where <USERNAMEOFREMOTECOMPUTER> is your computer (NOT NAS) username, XXX.XXX.XXX.XXX is the IP Address or hostname of your computer and <NAMEOFYOURSHARE> is the shared folder name. You should be prompted to enter your PC’s password to connect.
This creates the /mnt/rescue-share directory on your NAS and mounts the shared folder to it, then switches to that directory so you’re now inside that shared folder connected from your NAS. You can test it by entering touch hello to make a file called hello if you like.
Using the examples in step one, my command would be:
sudo mount -t cifs -o user=Tulip //MY-PC/qfix /mnt/rescue-share
5. Enter the command uname -a and the prompt should return some text like:
Linux <NAS_NAME> 4.14.24-qnap #1 SMP Tue Mar 2 06:10:10 CST 2021 x86_64 GNU/Linux
Make a note of whether this text contains i386 or x86_64 near the end, which is your NAS’ architecture. We need this to choose the appropriate download for the next step.
6. Download the testdisk tool for your NAS’ architecture by entering one of the following commands:
i386: wget https://www.cgsecurity.org/testdisk-7.2-WIP.linux26.tar.bz2 -O testdisk.tar.bz2
x86_64: wget https://www.cgsecurity.org/testdisk-7.2-WIP.linux26-x86_64.tar.bz2 -O testdisk.tar.bz2
This will download a file called testdisk.tar.bz2 to your shared folder.
7. We need to decompress the tool. Use the command tar -xvf testdisk.tar.bz2 to do that. This will unpack it into a new folder, you’ll have to check exactly what it’s called by using the command ls or looking on your shared drive from your computer but for me it was testdisk-7.2-WIP. Go into that folder by typing cd followed by the folder name (e.g. cd testdisk-7.2-WIP). Once there, we need to change the permissions of the test tool so that we can execute it, do that by typing chmod +x ./photorec_static
8. We need to get the volume for your compromised drive. You can find it by entering the command df -h. Unfortunately this will differ NAS-to-NAS but if you haven’t got any particular wild setup, you’ll probably be looking for whatever is mapped to share/CACHEDEV1_DATA on the right hand side. Here’s an example output where the volume can be found to be /dev/mapper/cachedev1 (note: personally, this was the same for me!)
Example output:
Filesystem Size Used Available Use% Mounted on
none 300.0M 272.7M 27.3M 91% /
devtmpfs 938.4M 8.0K 938.4M 0% /dev
tmpfs 64.0M 3.1M 60.9M 5% /tmp
tmpfs 949.7M 156.0K 949.6M 0% /dev/shm
tmpfs 16.0M 0 16.0M 0% /share
/dev/mmcblk0p5 7.7M 46.0K 7.7M 1% /mnt/boot_config
tmpfs 16.0M 0 16.0M 0% /mnt/snapshot/export
/dev/md9 493.5M 140.1M 353.4M 28% /mnt/HDA_ROOT
cgroup_root 949.7M 0 949.7M 0% /sys/fs/cgroup
/dev/mapper/cachedev1
898.3G 573.5G 324.3G 64% /share/CACHEDEV1_DATA
/dev/md13 417.0M 387.7M 29.3M 93% /mnt/ext
tmpfs 48.0M 72.0K 47.9M 0% /share/CACHEDEV1_DATA/.samba/lock/msg.lock
tmpfs 16.0M 0 16.0M 0% /mnt/ext/opt/samba/private/msg.sock
//XXX.XXX.XXX.XXX/share
1.8T 104.7G 1.7T 6% /mnt/samba_spar_abo_share
9. Open the recovery tool by entering the command sudo ./photorec_static.
10. You will be prompted to select a volume. Select the volume you noted from step 8 (e.g. /dev/mapper/cachedev1)
11. You will be prompted to select a partition or the whole volume. Mine was ext4, select whichever ext appears for you (ext2/3/4)
12. You will be prompted to select another partition. Select the one labelled ext2/ext3
13. Final set of options. Choose the one labelled “FREE”
14. The last choice is where you want the recovered files to be saved. It should show you a directory listing of your current directory which will be inside the tool’s folder and you should see a lot of files relating to the tool. If you select the .. option this will navigate up one level back to the root of the shared folder. Press c to confirm the recovery folder.
15. That’s it! It will take quite a while depending on how big your drive is, You’ll see a lot of files you don’t recognise, likely logs, since it’s recovering -everything- that was ever deleted from that volume (so long as it hasn’t been overwritten by a new file). It also can’t save their names, so prepare for a lot of manual renaming!
Thanks again to the Reddit user Open_Bumhole and his permission to publish the steps above.
For those of you who are not aware of the QLocker ransomware and its effect on some people’s QNAP NAS systems, watch the video below.
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔
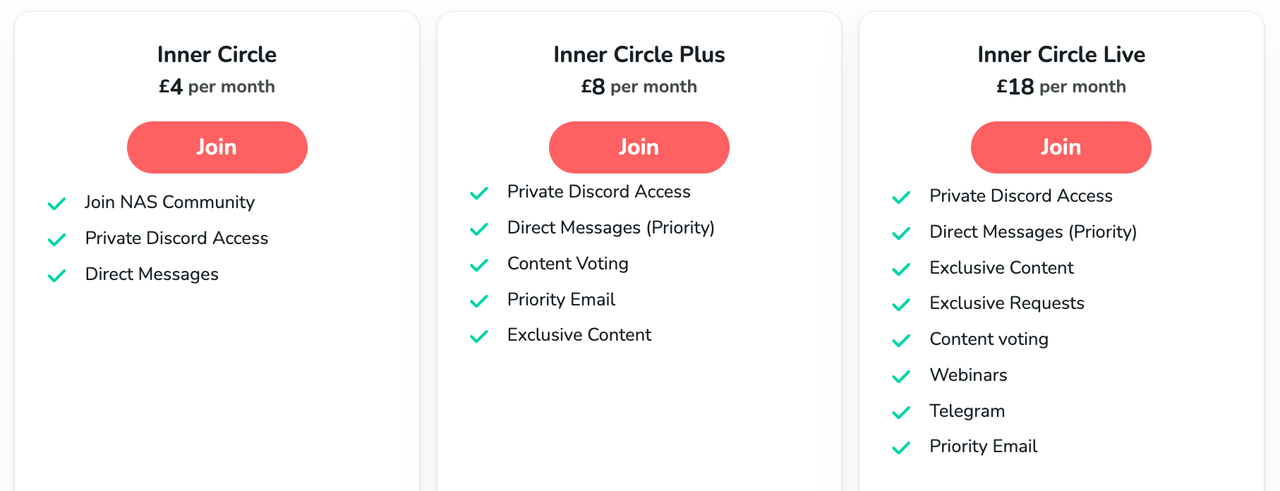
🔒 Join Inner Circle
Get an alert every time something gets added to this specific article!
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.

|
 |
ZimaOS is the BEST Beginner NAS OS - Watch Your Back UnRAID and TrueNAS !!!
30TB Hard Drives are TOO BIG ! (and here is why)
COMPLETE UGREEN NAS Setup Guide - 2025 EVERYTHING VERSION
$110 USB4 to 2x10Gb Adapter Review - What the WHAT?
UGREEN NAS Now has iSCSI, 2FA and Jellyfin (and more) - FINALLY!
Seagate 30TB Ironwolf and EXOS Hard Drive Review
Access content via Patreon or KO-FI



Fantastic video. Thank you very much.
REPLY ON YOUTUBE
Great video with lots of good info. I have had my TS-853 Pro for 9 years now and I have not had any malware. I keep it off of the internet and always keep updates applied.
REPLY ON YOUTUBE
This video needs an update and to go a bit more in depth
REPLY ON YOUTUBE
Lots of things to check. I have noticed in the new version of 5.1.5 QTS. The login options include 2 step verification (password and OTP/authenticator) or passwordless (1 step) – last option is username and authenticator. I am thinking the 2 steps seems safer.
REPLY ON YOUTUBE
i was going to buy a nas— im not now
REPLY ON YOUTUBE
Please make an updated version of this video
REPLY ON YOUTUBE
This was a bit of a skimmy.
Overviews are one thing, but you did say you would show how to set this up securely. That wasn’t delivered here.
REPLY ON YOUTUBE
The more secure you make things, the harder it will be to manage and jump through to get what your after. You could use 2FA, and encrypt volumes, for single person or two, all of that really is not required.. as long as you have good passwords for each user., and just gets in the way anyway.
encrypted volumes also slow down you NAS as well, but depends on the CPU/RAM your NAS has. eg TS-451 would better than TS-251
I would prefer user-based folder access for security than 2FA just because 2FA and volume encryption works as a “whole” where as user password and permissions are “per-user”
Much more simple to manage. Many people may disagree, but its my NAS so… ???? Just make sure you use strong passwords and that’s it.. Also, its bad practice to keep changing passwords every 180 days,,
Companies used to do this in the past ,thinking it was more secure changing regularly, but all it REALLY did was ****** off employees.
Sorry, i manage my own security
REPLY ON YOUTUBE
not gonna lie I wasn’t thinking 20 minutes later all i’d hear is change password and scan for malware, that hardly keeps the NAS secure, if I had a good password to begin with my security isn’t increased by changing it constantly. and doing a malware scan isn’t keeping me secure, stopping malware get on my system would be. and being notified of the lack of security is moot and not keeping me secure. password, update and scan malware. that takes 20 seconds. I thought you were going to show us how to disable certain ports, etc.
REPLY ON YOUTUBE
Very BASIC security settings but the best security for QNAP is to keep all services OFFLINE completely so I absolutely NEVER use QNAP Cloud!
As of January 2023 QNAP still has major online security issues so I will not trust QNAP online servers, nor cloud services and especially not email notifications handled by QNAP.
For email notifications to be sent…QNAP needs QNAP email servers. Today QNAP products are still vectors for ransomware so please Do NOT connect to QNAP servers!
Novice QNAP users should be offline ONLY, therefore should not be using notifications nor QNAP Cloud.
REPLY ON YOUTUBE
Is myqnapcloud the only thing that “connects us to the internet.”
So my question is as long as I disconnect from myqnapcloud then a large majority of my risk goes away?
REPLY ON YOUTUBE
Can you do a video with the best firewall configuration for a multimedia qnap server like the tvs h674 without using the upnp method?…. thanks again.
REPLY ON YOUTUBE
I was hit by deadbolt ransomeware some weeks ago. Finally I got the key and my files have been fully decrypted. Thank you…
REPLY ON YOUTUBE
Have you done a video on how to set up let’s encrypt SSL for secure remote access to a NAS?
I’m just a simple Plex user and moved awhile ago, that whole time my Nas was unplugged and unused for 2 years and I recently plugged it back in after setting up a media room. My NAS wouldn’t update firmware so I updated it manually with a flashdrive and I needed to make a whole new mycloud account for some reason. It’s been a pain getting it all set up but it’s currently in sleep mode. Am I still safe?
I did manage to set up 2FA on admin and basic user account and I’ll see about setting up the X failed password revoking privileges
REPLY ON YOUTUBE
Hello sir .. recently (3 weeks ago) I brought home the QNAP TS-673A NAS. It is my first. I am a musician, looking for a less complicated, faster data throughput option mainly to avoid the audio sample libraries’ often AGONIZINGLY slow loading times. (The ‘less-complicated’ meaning that, I don’t want a setup like my current – every USB port on my laptop taken, including the Thunderbolt4 port acting as a “super-fast 3.1 Gen2 interface” to a StarTech Gen2 hub, with 4 short Gen2 cables out to portable WD Gen2 drives…) YES, it’s a nightmarish mess, but gets me the speed I want. But when I update the Kontakt library database for example, I need to scan 5 folders on 5 separate drives – instead of just 1, which I hope to achieve, and with similar speed, in my new QNAP setup.
This would be up and running a few weeks ago, but I am busy touring with the band I play with this summer and seldom home on weekends. But in my research about QNAP NAS’s (including, thankfully, many of your fine contributions here on YT) .. it didn’t take long at all to learn of the security exploits and dreaded RW attacks. So my ‘rush’ to setup this NAS – turned into something not so rushed at all. One alternative, according to a review of my same product on Amazon, indicates the fellow used something called “TrueNAS Scale” – a freeware, open-source OS he claims to be much more secure than what QNAP offers, but what others say is incredibly complex and non-user-friendly.
So right now, I sit on a day off with the NAS plugged in (not powered on) populated with 1 WD “Gold” Enterprise 8 TB drive, along with 4 WD “Red Plus” NAS 8 TB drives, ready for a RAID 5 configuration. My laptop’s Thunderbolt 4 port is connected to one of the NAS’s USB faster ports (not the slower USB-C which you rightfully ridiculed in your TS-873A review). The ‘Power’ button has not been pushed yet. I have a network connection ready for a cloud install when I finally turn it on, and I have your 2022 QNAP NAS Setup Guide series of 6? videos all cued up and ready to follow with precision. So I guess my only question is: IS IT SAFE, on this day, TO DO THE STANDARD QNAP QuTS “hero” install??? Or should I try the alternative TrueNAS Scale install, for which there are a few walkthrough videos I could follow as well? I’m leaning toward QNAP … but only if it is safe. Answers from anyone well-experienced NAS’ers are welcome too. Thanks you sir, and keep up the great work you do!
REPLY ON YOUTUBE
You didn’t mention running a VPN. 🙁 That saves so much complexity.
REPLY ON YOUTUBE
Worker with a reliable hacker is what I think is all over the world and I recommend a hacker parfait who works with good heart and sincerity Dee_hack11 is in Seoul☝️☝️☝️.
REPLY ON YOUTUBE
If i don’t have QNAP Cloud installed, does that mean that i am not connected to the internet?
Is sending email notification not a good idea, considering i don’t want to link my NAS to the internet?
REPLY ON YOUTUBE
The best person to contact is #GLOCYBER ON INSTAGRAM he got all the ideas on each of the virus extension. He was able to repair mine.
REPLY ON YOUTUBE
It has been a week when I got infected but today I saw a comment that recommended me to #GLOCYBER ON INSTAGRAM and he was able to open all my files.
REPLY ON YOUTUBE
My MacBook was affected and I had no option than to contact #GLOCYBER on instagram. He did helped me recover all my files.
REPLY ON YOUTUBE
I suggest you should all contact #GLOCYBER ON INSTAGRAM. He was able to help me fix my computer.
REPLY ON YOUTUBE
My company system was infected too. We all couldn’t use our computers because it spreads to everyone computer. Our manager has explained that he hire #GLOCYBER ON INSTAGRAM and he was able to fix it. At least, we could have our jobs again.
REPLY ON YOUTUBE
My mums computer was infected and she asked me to help her. Although I don’t know how to fix it so I contacted #GLOCYBER ON INSTAGRAM and he helped us. He charged us a bit but it was very affordable. Thanks to him.
REPLY ON YOUTUBE
I got infected too. It was annoying seeing your computer but can’t use it. I did asked my technician and he suggest I should contact #GLOCYBER ON INSTAGRAM. I did contact him and he was able to help me out.
REPLY ON YOUTUBE
Am a photographer and it affected all my clients files and pictures. It affects my animal documentation pics. I almost cried, then I make my research and found out that #GLOCYBER ON INSTAGRAM has been helping out. He did mine and thanks to him.
REPLY ON YOUTUBE
Thanks to #GLOCYBER ON INSTAGRAM. He was able to fix my computer and all my files are normal.
REPLY ON YOUTUBE
My NAS was attacked by the virus but I was able to reach out to #GLOCYBER on INSTAGRAM and he could figure it out.
REPLY ON YOUTUBE
I got affected by the division of the virus. And I could not read for my exam because it encrypted all my lectures note. Thanks to my lecturer who recommended #GLOCYBER ON INSTAGRAM to help me recover my files. He did and am so happy.
REPLY ON YOUTUBE
Am a student too and it lock all my pdf and everything other thing in my laptop. Am so happy I got help from #GLOCYBER ON INSTAGRAM. He did a marvelous work and now I have all my files back.
REPLY ON YOUTUBE
I recommend you all to contact #GLOCYBER ON INSTAGRAM. He was able to help me recover all my encrypted files. Am glad I met him earlier.
REPLY ON YOUTUBE
I was dead in need of my computer. But I could not all because of this virus. I was recommended to #GLOCYBER on instagram and he responded to me and helped me fix my laptop.
REPLY ON YOUTUBE
Am able to contact #GLOCYBER on INSTAGRAM and I showed him what has happened to my computer. He was able to assist and get my computer free from the virus.
REPLY ON YOUTUBE
I was affected too and I talked to #GLOCYBER ON INSTAGRAM . he could help and he did recover all my files and photo.
REPLY ON YOUTUBE
It was through the help of #GLOCYBER on instagram that we ware able to get our money photos decrypt. The virus has held all the pics in the system.
REPLY ON YOUTUBE
It was #GLOCYBER on instagram that was able to help me fix all my files and get them decrypt. He really did a great work and am happy I met him.
REPLY ON YOUTUBE
I found a legit cyber professional. He is #GLOCYBER on instagram. he was able to help me fix and decrypt all my encrypted files. Thanks to him for his kindness.
REPLY ON YOUTUBE
Contacting #GLOCYBER on instagram was the best thing I did after my files got infected. He quickly decrypt all my files and get me free from the virus.
REPLY ON YOUTUBE
This virus has been attached to my files for more than a week. It was my dad who directed me to #GLOCYBER on instagram and he was able to get rid of the virus. Thanks to him.
REPLY ON YOUTUBE
my files have been encrypted and I thought I would never use them again. My lecturer told me to reach #GLOCYBER on instagram and he was able to help me recover my files from the virus. Thanks to him.
REPLY ON YOUTUBE
Contacting #GLOCYBER on instagram was the best thing I did after my files got infected. He quickly decrypt all my files and get me free from the virus.
REPLY ON YOUTUBE
Am happy I could contact #GLOCYBER on instagram and he was able to help me remove all the virus. My exams files are free now.
REPLY ON YOUTUBE
My computer was affected too and it got stuck of all the virus. Thanks to my sister who had recommended #GLOCYBER on instagram. I search him on google and he responded to me. Thanks to him.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
…You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
…You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
.You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
.You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
Forgive that this may be a stupid question. But – if you have a QNAP NAS plugged in to your computer – and your computer is connected to the internet – does that mean your NAS is connected to the internet also? Or – is the hacking security risk purely for if you choose to directly connect the NAS to the internet (and therefore if you don’t, you risk free)?
REPLY ON YOUTUBE
????I was so glad when I finally realized and get in touch with Glo Cyber while I used the contact above. He is indeed a genius and his skill are authentic. I rec. everyone to appreciate his efforts.
REPLY ON YOUTUBE
will adding 2step verification change the way using share links work (ie: sending a share link to a shared folder on my nas to friends via email)?
REPLY ON YOUTUBE
People keep talking about Scott. I think he is good. I will try him.
REPLY ON YOUTUBE
Someone recommended you ????and you also helped me recover mine too. You a genius indeed
REPLY ON YOUTUBE
Someone recommended you ????and you also helped me recover mine too. You a genius indeed
REPLY ON YOUTUBE
Hi, Thanks for the great video!
Would you be able.to elaborate on sharing the file process to an external temporary user, please?
REPLY ON YOUTUBE
Hi, Thanks for the great video!
Would you be able.to elaborate on sharing the file process to an external temporary user, please?
REPLY ON YOUTUBE
I miss the most important step, formatting and throwing away the QNAP.
REPLY ON YOUTUBE
You’re ???? such a genius, I really appreciate your services, fast and safe recovery process.
REPLY ON YOUTUBE
Found the presentation very irritating. Why keep wizzing the cursor around the screen. Why not use a large black cursor. Don’t do everything so quickly.
REPLY ON YOUTUBE
Just come here because my NAS has been compromised! I’m so annoyed and this has been a major blow for my business (video production company).
REPLY ON YOUTUBE
I have an older TS-469 Pro running 4.3.4, so I guess my NAS is somewhat obsolete in terms of available applications such as Security Counselor
REPLY ON YOUTUBE
I don’t have the QuFirewall and the SSecurity Counselor available sadly, at least it just doesn’t want to install. Probably because my NAS is way too old, running QTS 4.2.6
REPLY ON YOUTUBE
People should know about this this is madness, just happenned to me? 8 months later?? Could they have warned their F*ing customers??!!
REPLY ON YOUTUBE
WOW. Nice find here!! Great video.
REPLY ON YOUTUBE
Thank you. Wish I’d seen your recommendations BEFORE the Qlocker attack.
REPLY ON YOUTUBE
i was infectet now on 7 dec 21
REPLY ON YOUTUBE
I don’t use my over the cloud I only use it with my local network. Is it safe that way ?
REPLY ON YOUTUBE
hello sir your videos is so helpfull for me but i am confuse with how to configure alnet ssystem software with qnap nas storage i have configure qnap nas storage raid 6 with 4tb *12 hdd 1 hdd in spare but i am able to see live video but not able save nas storage so can you help me how to add path in qnap nas storage for save recording. Thanks,Jerry Upadhyay
REPLY ON YOUTUBE
If Norton or Bitdefender is installed as your main antivirus, will they be able to work on Qnap NAS? Instead of MacAfee, which for instance I don’t like.
REPLY ON YOUTUBE
Dude. Just a side note after watching 150+ videos. I have NEVER heard “noise in the background” so please stop apologizing for it. Not. Once. Ever.
REPLY ON YOUTUBE
The little graphics was very helpful. I learned my lesson for sure on what having a backup actually means.
I naively bought my NAS thinking it would be my own little personal cloud machine and sole backup (thinking raid would keep me safe forever) for my documents, photos, and videos.
Now I realize I’m going to still have to spend more money on cloud services and be very careful with my qnap nas.
I was immediately thinking of switching to Synology since you said it’s more user friendly and all I really use my NAS for is backup and as a cloud drive to put my files into it and be able to retrieve them on my phone. Unfortunately, from what I’ve seen on the appstore the other Nas company apps look like they are just as rough, slow, and confusing to use as Qnap’s (Qmanager and Qfile). I don’t understand how “downloads” and “Qsync” works on Qfile for example so I’ve been just moving files manually as I would on any other cloud app.
For now I’m staying with my TS-453D.
But still have mixed feelings about it.
REPLY ON YOUTUBE
I wish I saw this video before ???? apparently Qnap got hit with a massive ransomware attack this year and I had no idea. My files are all encrypted by some hacker asking for Bitcoin in exchange for passwords ????
REPLY ON YOUTUBE
So I got stung by the Qlocker ransom ware attack and apparently it was caused by a back door issue relating one of the apps, hybrid desk station? I can’t recall I was too busy fuming at how a company could have this vulnerability. And I do appreciate the support the qnap staff have tried to give in recovering the files and data, but when the process broke down and they let communication fade, with lack of support to get a resolution I soon lost patients with them and decided to let go of some files. I thankfully did have back ups but when your sync does the backing up it basically just had a knock on effect so ran some files where synced to pc, and a back up hard drive before I had noticed. Thankfully larger files where left and they only went after the smaller file sizes.
Anyway long story short, always back up your data manually on an off line hard drive. This is the only real way you can secure a true back up of your files. Thankfully an old NAS gave that option to me.
REPLY ON YOUTUBE
Changing the default port does not enhance security. Security by obscurity. Port scanners can detect open ports it might fool some scripts.
Most people who serious about securing administrative interfaces dont expose them directly to the internet period.
Thats terrible terrible terrible security pratice.
A seperate vpn server with a dedicated vlan for admin is what you should be using to secure the admin interface and remotely managing the nas.
Example
Setup vlan 100 for management
Setup vlan 201 for cifs
Setup vlan 202 for iscsi
Setup vlan 300 for public network (internet)
Setup vpn server in dmz with one arm into the public network (300) another arm into vlan 100.
Setup logging and auditing.
Ensure 2fa exists for vpn service.
The qnap should have ports trunked with vlan 100,201,202 or dedicated ports.
Assign the services ip addresses in each of the ranges.
I never ever bother changing port numbers it simply offers very little security and may just elude some scripts scanning on certain ports
REPLY ON YOUTUBE