The Current Synology & QNAP NAS and OpenSSL Security Issues Explained
As many of you may have heard, in recent weeks there were two vulnerabilities identified in the OpenSSL encryption platform, a popular SSL option for many sites and servers, that provided an opening for particularly industrious interlopers to access a site via a weakness in the platform. Although not a service that is developed by Synology or QNAP NAS, it is used in several smaller areas/applications in their respective DSM and QTS software platforms. This is not uncommon for a brand to use a third-party provider and OpenSSL is one of the most popular open-source SSL platforms in the world. This vulnerability in OpenSSL was identified in late August and although alot has happened in that time, though the vulnerability is beginning to be resolved, it is still not fully resolved on the Synology or QNAP NAS affected software and services. So, today I wanted to go through what an SSL is, what OpenSSL is, the nature of the vulnerabilities, what has been resolved, what hasn’t and ultimately explain where things are right now. Let’s get started!
What is an SSL certificate?
You know when you browse the internet and there is that little padlock next to the www.website bit? That symbol indicates that communication between your web browser and the website/server you are communicating with is encrypted. This padlock identifies the SSL certificate, or Secure Sockets Layer and in recent years it has become heavily encouraged that any website you visit has a valid and secure SSL in place (with google warning you if you go to an ‘unsecure’ site and openly recommending SSL engaged sites higher on page 1 of Google. If you are choosing to access your NAS via the internet, then then it is recommended (and set as a default on the NAS platforms in many ways) to access your server via an SSL equipped connection, as this adds a valuable security protocol and creates an encrypted link between a web accessed server and a web browser.

What is OpenSSL?
OpenSSL is a open-source encryption tool/library – released in 1998 and REGULARLY updated, it is regularly used by both Synology and QNAP in a number of their software and services that feature a remote access component. It is not just them and many, MANY others use OpenSSL in PARTS/ALL of the architecture of their remote connections for encrypted data transfers. The use of OpenSSL is by no means a negative mark on any brand, as it has been developed over an exceedingly long time and is regularly updated.

What was the Vulnerability with OpenSSL?
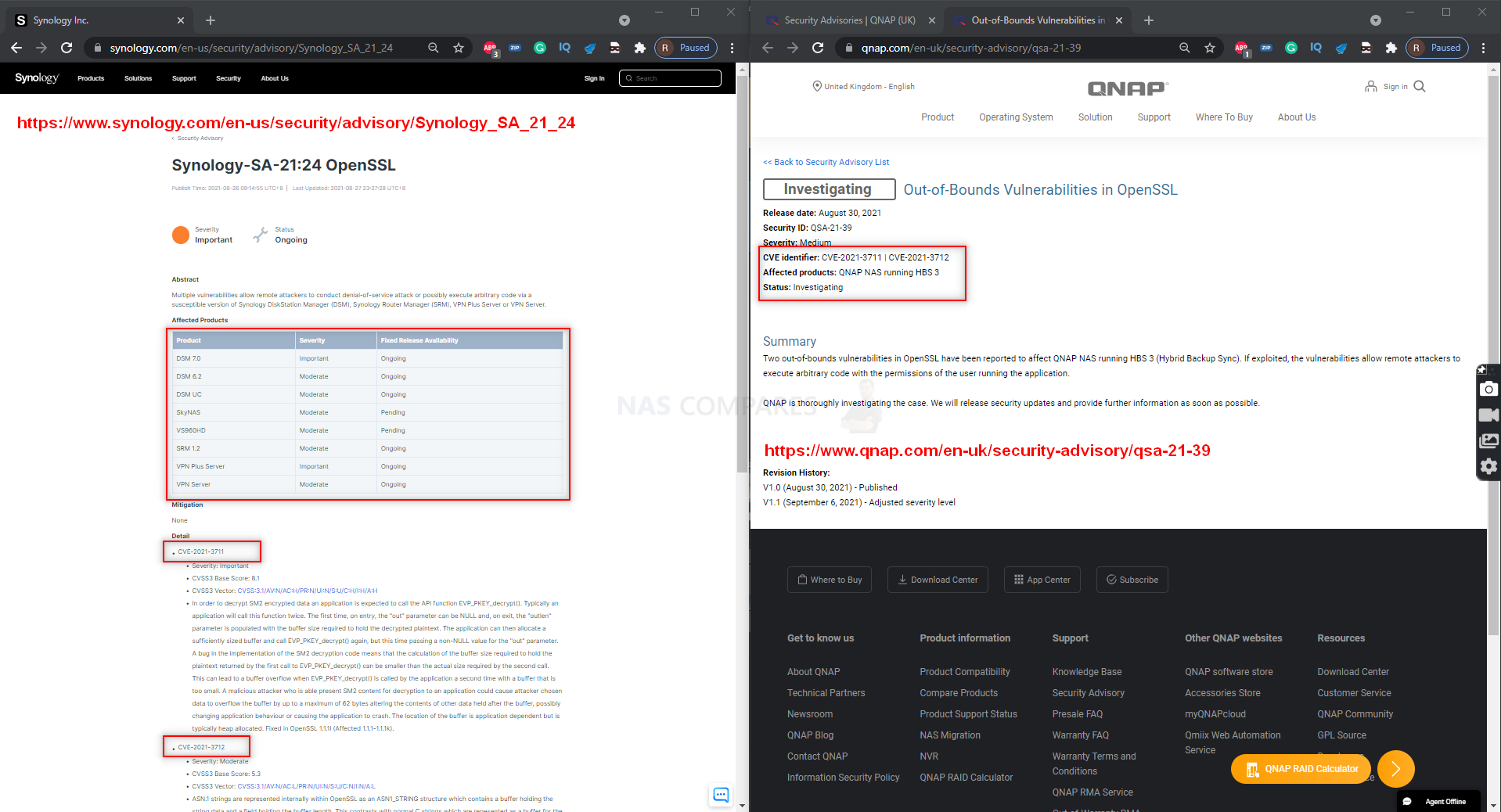
In August, two vulnerabilities in the OpenSSL platform were identified and OpenSSL themselves were contacted immediately. The “CVE-2021-3711” and “CVE-2021-3712” security holes were in the as-then-latest release of OpenSSL and in their own security updates and advisory, were listed as Moderate and Severe in importance. Likewise, OpenSSL (among others no doubt) contacted Synology and QNAP to highlight this vulnerability and each brand added entries into their security advisory and posted on their own platforms about this, adding that they were working on a resolution (almost certainly to be based on the resolution formed and executed by OpenSSL themselves). The two vulnerabilities were still remarkably small and required a rigid-set scenario and knowledge in order to be in any way usable. However, they did open the door to the following negative actions and allowing attackers to:
- Carry out DoS attacks on the server
- Execute malicious code into the server
- Gain remote access to the Server through a buffer overflow.
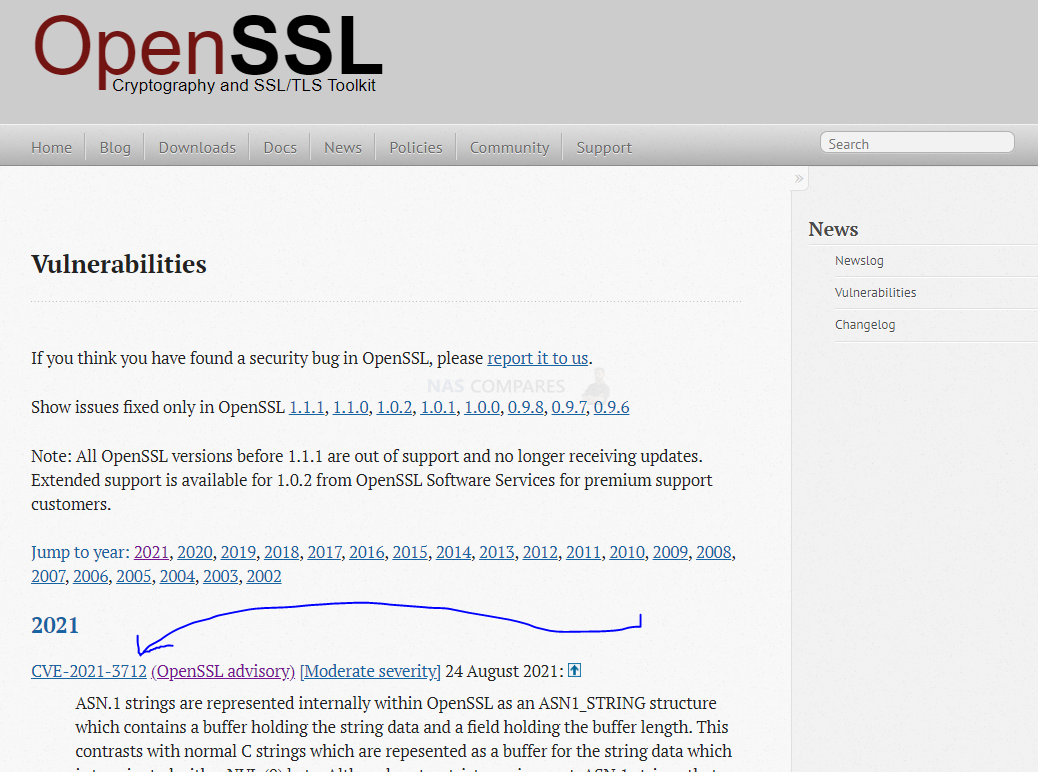
In the case of Network Attached Storage (NAS) from the likes of Synology and QNAP, it was highlighted very early on that it could only effect NAS systems with internet connectivity. On August 24th 2021, OpenSSL was able to resolve these vulnerabilities, closing the matter and issuing a patched update to OpenSSL that removed them both. However, at the time of writing, both vulnerabilities are listed as ongoing on both the Synology and QNAP Security Advisory page (where they highlight any/all security issues on their platforms that have been resolved/worked on).
[youtube https://www.youtube.com/watch?v=jzfKb-5h1XM]What Is Synology NAS Doing About the OpenSSL Vulnerability?
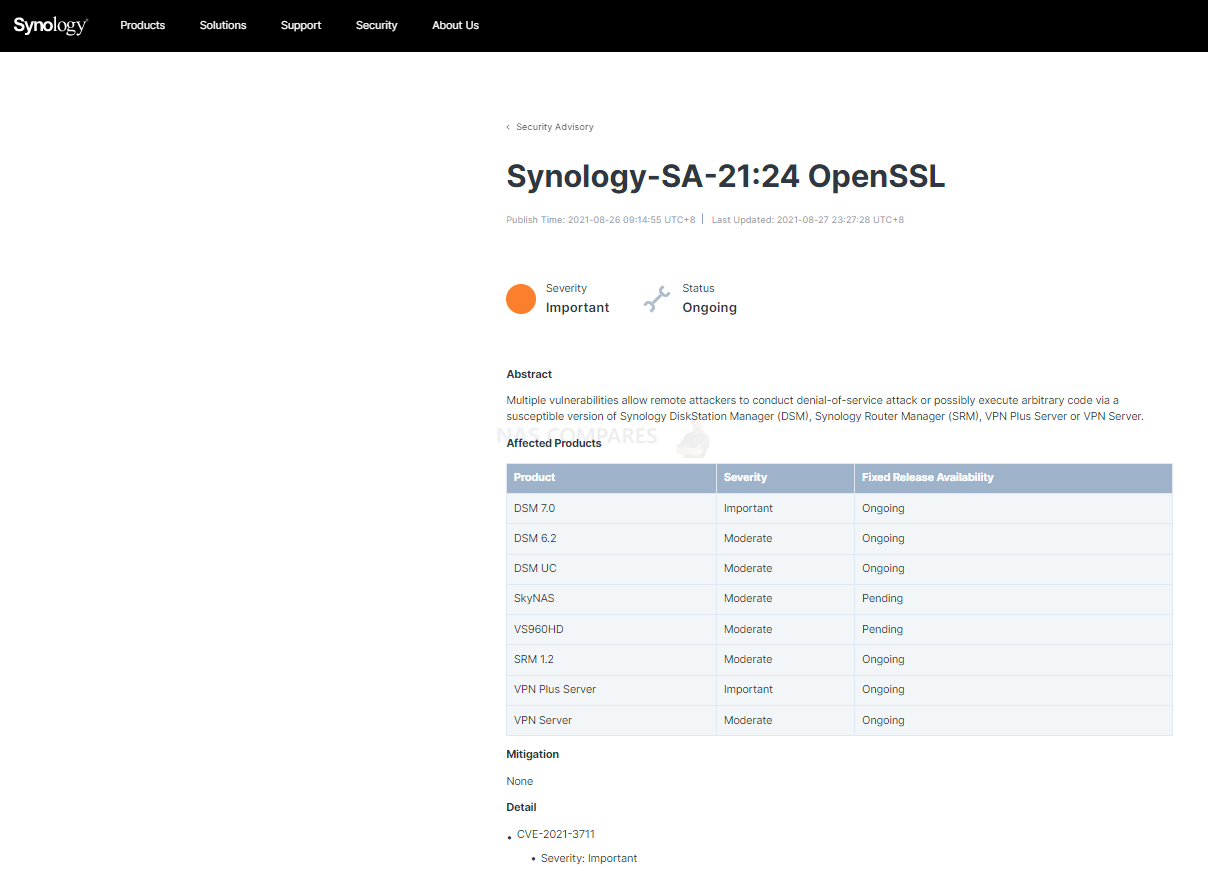
Both Synology and QNAP have been updating their users on the resolution of these OpenSSL vulnerabilities, though both brands have yet to implement a full fix at this time for all vulnerabilities across their software platforms. Given that both brands use a unique/modified version of Linux to create their software and services, a simple application of the OpenSSL fix issued on the 24th August is likely incredibly difficult and modification, application and testing of any resolution needs to be conducted by both internally before a widespread software update is issued. While Synology or QNAP does not provide an estimated timeline for these incoming updates being fully concluded, last month Synology told BleepingComputer that it generally patches affected software within 90 days after publishing advisories. Fairplay to Synology publishing information on this immediately.
| Product | Severity | Fixed Release Availability |
| DSM 7.0 | Important | Ongoing |
| DSM 6.2 | Moderate | Ongoing |
| DSM UC | Moderate | Ongoing |
| SkyNAS | Moderate | Pending |
| VS960HD | Moderate | Pending |
| SRM 1.2 | Moderate | Ongoing |
| VPN Plus Server | Important | Ongoing |
| VPN Server | Moderate | Ongoing |
Indeed, below is a statement issued online from Synology to be.hardware.info responding these vulnerabilities and why the brand is handling them internally this way (translated from German to English):
Synology-SA-21:24 OpenSSL includes two vulnerabilities, CVE-2021-3711 and CVE-2021-3712.
CVE-2021-3711 does not affect most Synology devices as they do not use SM2 encryption by default. Although our NAS devices are currently sold with an affected version of OpenSSL, there can only be said to be a security risk if administrators use third-party software with SM2 encryption.
CVE-2021-3712 addresses specific functionality related to the creation of x509 certificates (used for security protocols such as https) that may cause denial-of-service on the affected device. It is difficult to abuse this as it requires administrator privileges.
Furthermore, the manufacturer emphasizes that the priority of updates is based on the frequency of the affected configurations, the complexity of exploiting the vulnerability and the extent of the potential damage that can be caused. In its own words, it should be sufficient to remedy the aforementioned risks within the usual 90-day period.
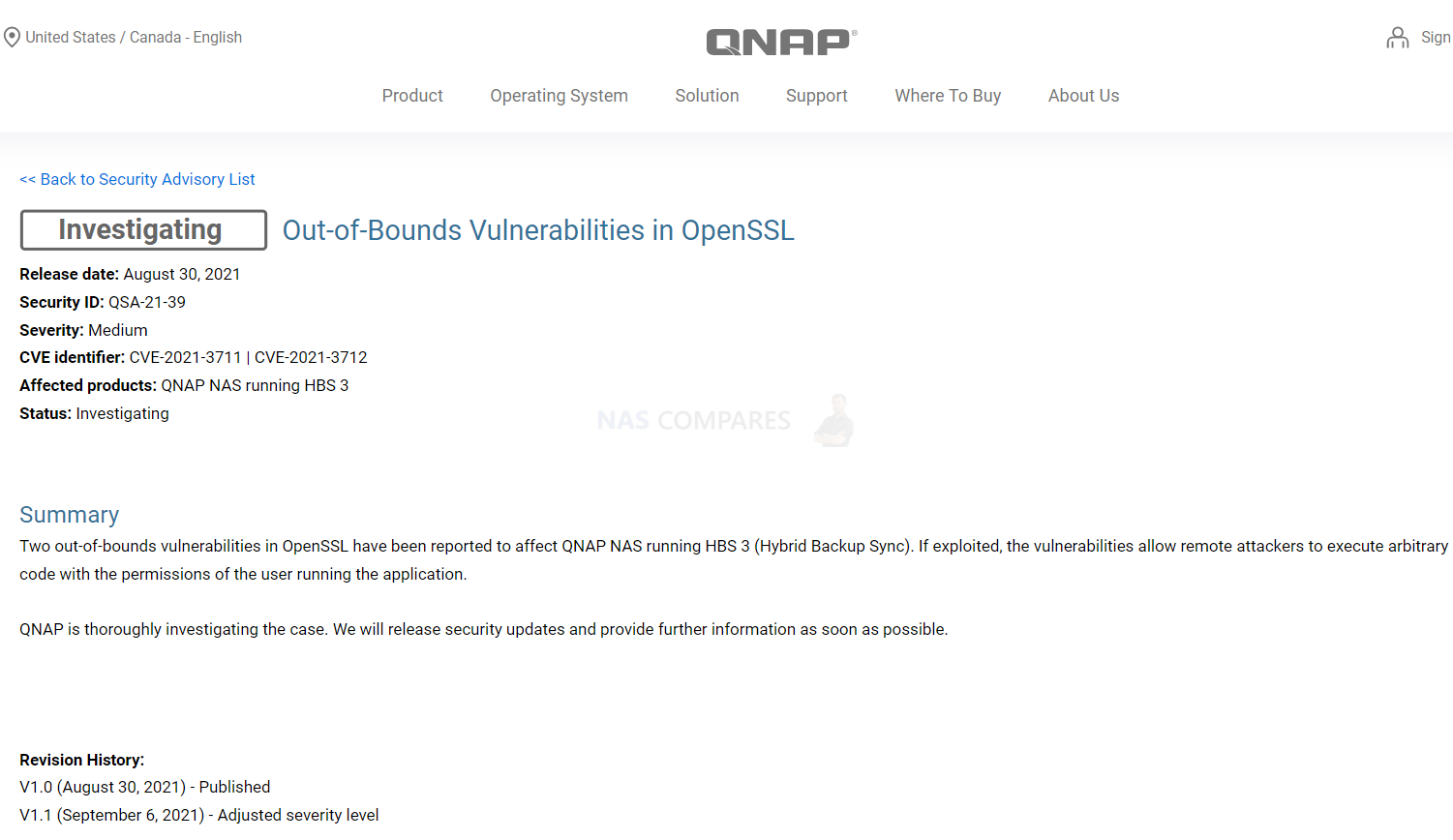
What Is QNAP NAS Doing About the OpenSSL Vulnerability?
QNAP stated on their own security advisory last month the following two potential consequences of these vulnerabilities if pushed to their fullest extent:
An out-of-bounds read vulnerability in OpenSSL has been reported to affect QNAP NAS running QTS, QuTS hero, and QuTScloud. If exploited, the vulnerability allows remote attackers to disclose memory data or execute a denial-of-service (DoS) attack. Additionally, an additional out-of-bounds vulnerability in OpenSSL has been reported to affect QNAP NAS running HBS 3 (Hybrid Backup Sync). If exploited, the vulnerabilities allow remote attackers to execute arbitrary code with the permissions of the user running the application.. QNAP is thoroughly investigating the case. We will release security updates and provide further information as soon as possible.
How To Stay Informed on Synology & QNAP NAS Vulnerabilities?
At NASCompare we provide a regularly updated list of current vulnerabilities and security issues as they are published on the respective QNAP and Synology Security advisors.
You will find. list in this article:
Vulnerabilities, Ransomware and Exploits on Synology & QNAP NAS – Stay Updated!
And Lastly, please, please, please:

Need Advice on Data Storage from an Expert?
We want to keep the free advice on NASCompares FREE for as long as we can. Since this service started back in Jan '18, We have helped hundreds of users every month solve their storage woes, but we can only continue to do this with your support. So please do use links to Amazon Amazon UK on the articles when buying to provide advert revenue support or to donate/support the site below. Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you.
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you.
 Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
 Home: https://www.backblaze.com/cloud-backup.html#af9rgr
Business: https://www.backblaze.com/business-backup.html#af9rgr
Comparison with other service providers: https://www.backblaze.com/best-online-backup-service.html#af9rgr
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔
Home: https://www.backblaze.com/cloud-backup.html#af9rgr
Business: https://www.backblaze.com/business-backup.html#af9rgr
Comparison with other service providers: https://www.backblaze.com/best-online-backup-service.html#af9rgr
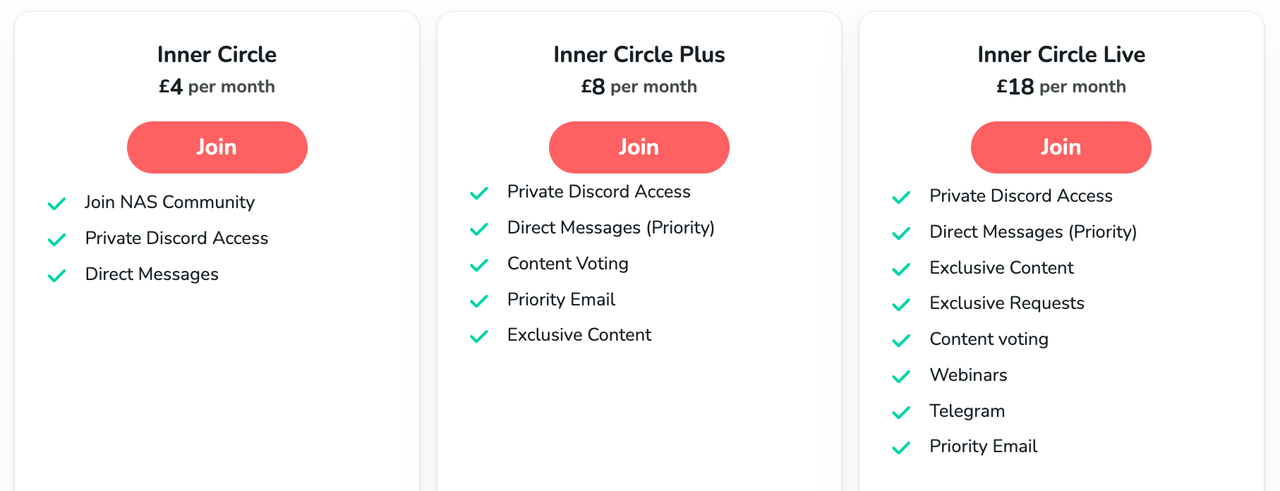
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔🔒 Join Inner Circle
Get an alert every time something gets added to this specific article!
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.

|
 |
Minisforum N5 Pro NAS - Should You Buy?
UGREEN DH4300 & DH2300 NAS Revealed - Good Value?
Aoostar WTR Max NAS - Should You Buy?
Xyber Hydra N150 NAS Review - Is This COOL?
Minisforum N5 Pro vs Aoostar WTR Max - The BIG Showdown
Do MORE with Your M.2 Slots - GREAT M.2 Adapters!
Access content via Patreon or KO-FI








Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
7:45 Your right… It IS a gross analogy..,,,
REPLY ON YOUTUBE
Thats the deal with Open Source…. Millions more devices need to, be updated and often lag behind others.
Much similar in the non-open source world when only a handful of devices use Microsoft, Adobe and Google stuff..
To be fair, blame all of us for “wanting” to connect to remote locations to begin with .. If no one wanted it, it wouldn’t be as useful, but then much less security issues as well. You may argue some may no longer be “important” because its not affected as much either, also eventually you’d still wanna get around to patch getting out/applying
REPLY ON YOUTUBE
…… what is the best 2bay nas in terms of price performance and reliability? …and is the ds720+ usable at the same time with 2xhdd and 2xssd?
REPLY ON YOUTUBE
What does liquacious mean
REPLY ON YOUTUBE
Autoblock and geofencing is a must go web connected synologies.
REPLY ON YOUTUBE
Thankyou for the Video @Nascompares We all do are Bit to help each other out and get the info out there so we can keep are data safe and know where we stand Thanks Robbie
REPLY ON YOUTUBE
Thank you, great message but security stuff makes my brain hurt, not the sharpest tool in the shed here. Cheers
REPLY ON YOUTUBE
It’s ok, no personal loot, but then they should add player difficulty online
REPLY ON YOUTUBE
So you just compared the home NAS to a toilet. Well done, Robbie. ????
Maybe a better analogy would be the lock on your bedroom door rather than your WC. I’m just sayin’.
REPLY ON YOUTUBE
Robbie, your sound and video are out of synch. Can you fix that? I’ve noticed it in several of your videos.
REPLY ON YOUTUBE
YouTube says one comment but I don’t see one. I’m guessing now it will say two but can only see mine.
REPLY ON YOUTUBE