Security Flaw in Ugreen NAS Certificates Under Investigation
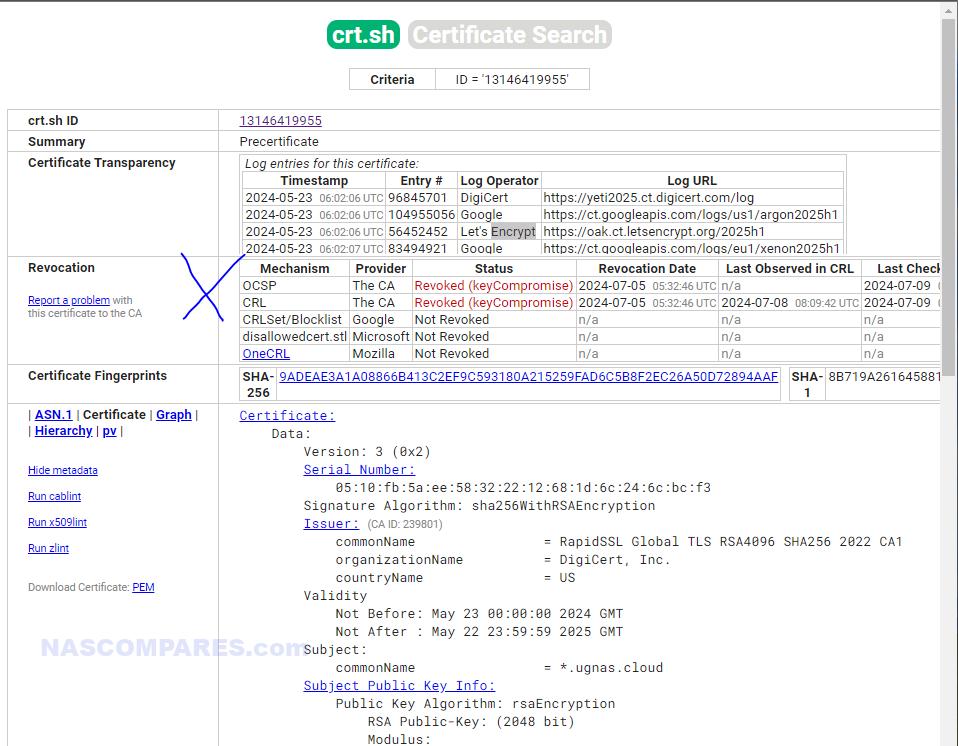
A security concern has been raised regarding Ugreen’s new NAS devices, sparked by a Twitter user in the East who claims that all Ugreen Private Cloud NAS users share a single certificate and private key. The tweet, shared by @realShellWen, has not yet been corroborated by other users or acknowledged by Ugreen. This issue is still under investigation, with Ugreen representatives contacted for comment but no response received yet. The tweet references a specific certificate on crt.sh, a site used to track and verify the status of SSL/TLS certificates.
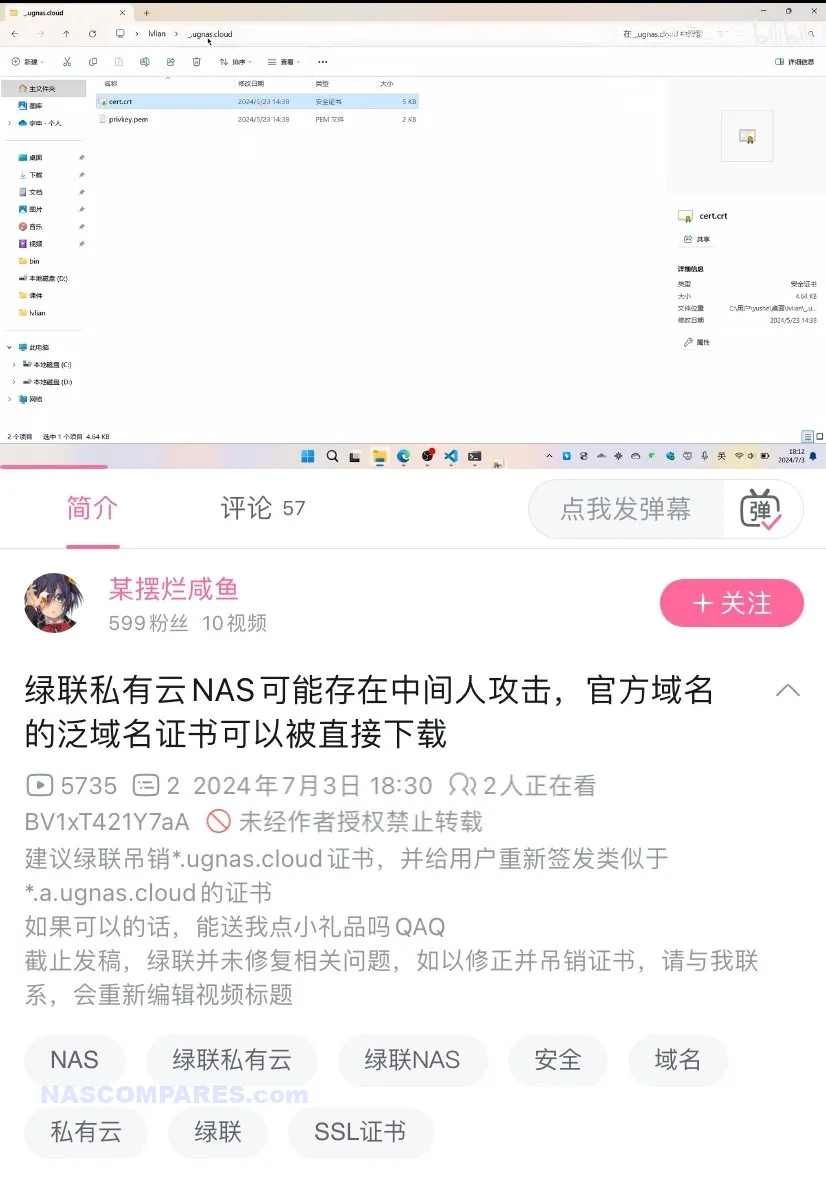
According to the crt.sh page for the certificate ID 13146419955, the certificate was issued on May 5, 2024, and has been revoked due to key compromise. Crt.sh is widely used by security professionals to monitor certificate transparency logs, allowing the public to check the issuance and revocation status of certificates. If the claim holds true, the use of a shared certificate could expose Ugreen NAS users to various security threats.
Generally, NAS brands handle certificates by issuing individual certificates for each device, ensuring that the compromise of one certificate does not affect other devices. They often use automated certificate management processes, such as the ACME protocol, for automatic issuance and renewal of certificates. This method minimizes the risk of human error and enhances security by providing unique certificates for each device, thereby maintaining the integrity of encrypted communications.
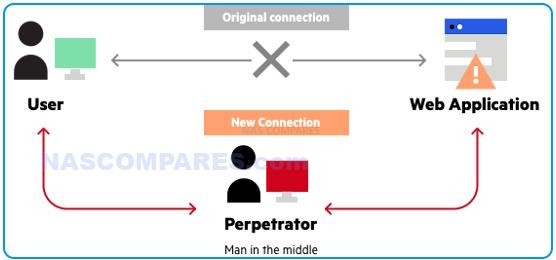
A shared certificate and private key scenario could enable man-in-the-middle (MITM) attacks, where an attacker intercepts and potentially alters communication between the user and the NAS. This could lead to sensitive data being compromised. Additionally, attackers could impersonate the NAS, gaining unauthorized access to data stored on the device. However, executing such an attack would require the attacker to be in a position to intercept the network traffic, which adds a layer of complexity to the exploit. Despite these potential risks, there has been no evidence of exploitation reported by other users or detected in user forums and discussions. If verified, the practical implications of this vulnerability could be severe. Shared certificates undermine the security architecture of SSL/TLS, as they essentially create a single point of failure. An attacker with the private key could decrypt traffic, impersonate the server, or conduct other malicious activities. However, it is important to note that this claim has so far only been raised by a single user. No similar complaints have surfaced in Ugreen NAS Reddit communities or on Kickstarter pages, where users frequently discuss and troubleshoot such devices.
To address this issue, if proven true, Ugreen would need to revoke the compromised certificate and issue new, individual certificates for each NAS device. This would prevent a single point of failure and ensure that the compromise of one certificate does not affect all users. Additionally, Ugreen would need to enhance their security protocols to prevent similar incidents in the future. This could include implementing automated certificate management processes, such as using the ACME protocol for automatic issuance and renewal of certificates, to minimize human error and improve overall security. Security experts recommend that companies use individual certificates for each device to prevent such vulnerabilities. This approach limits the impact of a single certificate compromise and helps maintain the integrity of encrypted communications. Users are advised to follow best practices, such as regularly updating firmware as it is issued (as this may well direct towards the installation of a new certificate if this is all true), using strong passwords, and monitoring network activity for any unusual behaviour and for any overt suspicious activity. Additionally, they should consider using a VPN for secure remote access and disable any unnecessary network services that might expose the device to potential attacks. The complexity and practicality of exploiting such a vulnerability depend on various factors, including the attacker’s ability to intercept traffic and the robustness of the network’s security measures. While the potential risks are significant, the actual threat level may vary based on individual user setups and configurations.

In conclusion, while the claim made on Twitter has yet to be confirmed by additional sources or official channels, it highlights a potentially significant security flaw in Ugreen NAS devices. The company’s response and the results of ongoing investigations will be crucial in determining the extent of the issue and the necessary steps to mitigate the risk. Users are advised to stay informed and await further updates from Ugreen regarding the situation. As the investigation continues, the community will be watching closely to see how Ugreen addresses these concerns and works to restore trust in their products.
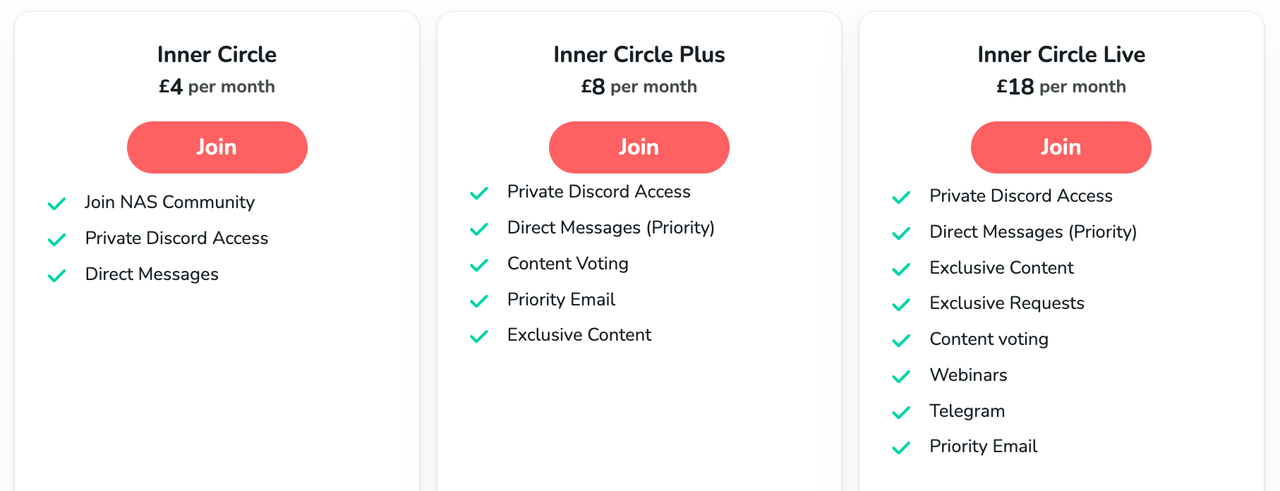
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔🔒 Join Inner Circle
Get an alert every time something gets added to this specific article!
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.

|
 |
| Where to Buy a Product | |||
|
|
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
 |
    
|

|
VISIT RETAILER ➤ |
We use affiliate links on the blog allowing NAScompares information and advice service to be free of charge to you. Anything you purchase on the day you click on our links will generate a small commission which is used to run the website. Here is a link for Amazon and B&H. You can also get me a ☕ Ko-fi or old school Paypal. Thanks! To find out more about how to support this advice service check HERE If you need to fix or configure a NAS, check Fiver Have you thought about helping others with your knowledge? Find Instructions Here
Minisforum N5 Pro NAS - Should You Buy?
UGREEN DH4300 & DH2300 NAS Revealed - Good Value?
Aoostar WTR Max NAS - Should You Buy?
Xyber Hydra N150 NAS Review - Is This COOL?
Minisforum N5 Pro vs Aoostar WTR Max - The BIG Showdown
Do MORE with Your M.2 Slots - GREAT M.2 Adapters!
Access content via Patreon or KO-FI




i need to sync/backup to Dropbox, multiple accounts, should i just go with Synology, even though they are limiting, HD , forcing to buy theirs, with their newer models?
REPLY ON YOUTUBE
Oh man can you do a vid on how to connect the a ugreen nas to a computer using 10gb ethernet?
REPLY ON YOUTUBE
It’s got the 2fa now. Great news uses Microsoft Authenticator. Could you do the other videos as I bought this due to your review. Thank you .
REPLY ON YOUTUBE
I have a DXP8800 bought on Dec 11, 2024, Here is what I have found.
The system has a bad “coil whine” that appears to come from the power supply, NOT the fan.
The fans in “Default Mode” and the system in idle mode can’t cool 8 HDD below 110f, in “performance mode” there is no way you can call this a “Desktop NAS” unless you are Deaf.
The 10GB Net cards are a joke as the most transfer rate I have seen is about 400MB. They need to prioritize the MTU change to 9014 and allow Jumbo Frames.
I have 64GB memory and 1TB of M.2 drive and tried using them (M.2) as caching only to find the file transfer will actually “Studder”.
I have all 8 bays filled with the Seagate 2X18, 18TB Mach-2 HDD with dual actuators. I have half configured in Raid 5 and the other 4 in Raid 0.
I have changed all the performance settings in the OS to achieve the best performance, with little to no change.
My Desktop system is running an I-7 running at 4.0GHZ, 64GB Memory, and a dual port 10GB genuine Intel (550 chip) Net card, all Net cables are Cat-8.
I have tried transfering from a 4 SSD raid-0 to and from the NAS with not much better results at to speed.
I tried transferring 9GB of data to the NAS and it took 36 hours to complete.
Even transferring from one storage pool to another is much slower the expected.
I do believe the entire problem is within the OS’s ability to handle the transfer rates of SATA-3.
So I shall load another OS M.2 and try TrueNAS and possibly UnRaid next.
REPLY ON YOUTUBE
It’s sus
REPLY ON YOUTUBE
would be better of software was open source. what backdoors are there?
REPLY ON YOUTUBE
Can UGOS catch up to DSM soon? Consumers really need a shake up in the space.
REPLY ON YOUTUBE
Lopez Kenneth Perez Timothy Lee Matthew
REPLY ON YOUTUBE
Robinson Nancy Clark Carol White Jennifer
REPLY ON YOUTUBE
I don’t understand NAS hardware vendors’ obsession with making subpar software that their clients will have to subsidize
REPLY ON YOUTUBE
You know, I just can’t help getting the feeling that doing a preinstall of truenas would have just been a better option. I get why they did it from a market/business perspective, but it feels like until the segment was more built and mature for them, sticking truenas or unraid (though, unraid has its own cons related to annual/lifetime license charges) as the os would have been a wiser move initially. They could have then taken the first several models as they grew to understand what is wanted and better tailor an os to the market instead of charging off first run like this.
REPLY ON YOUTUBE
Some avi file don’t play correctly using the ugreen app. However, using Windows file manager and vlc app the files play correctly.
REPLY ON YOUTUBE
Time for a new review!
REPLY ON YOUTUBE
Lopez Ronald Walker John Young Lisa
REPLY ON YOUTUBE
Marguerite Extension
REPLY ON YOUTUBE
just install debian and be done with it
REPLY ON YOUTUBE
Felipa Ramp
REPLY ON YOUTUBE
Will Plex be adding native support to Ugreen without the need for docker?
REPLY ON YOUTUBE
What OS would you recommend if this os isn’t great, for a noob as well lol
REPLY ON YOUTUBE
These other companies are holding us up with a tier system. Ugreen has seen a massive hole in these companies holding us to ransom and not giving the consumer what they want at a reasonable price . Too many variants without top end performance . Things have changed now spinning hard-drive are becoming more affordable. All I want is the highest spec CPU for 4k plex, with high end expendability for memory, cache ,and ethernet . It doesnt need to be high end memory etc at time of purchase because we can always upgrade. It is that simple. High end chip with expandability at consumers expense .
REPLY ON YOUTUBE
Hi there @nascompares. Love your videos… They’re super informative and unbiased. I see that Ugreen NAS are hitting the market (can be purchased in Germany now). Are you planning an updated review with the production version of UGOS? Have you heard of any planned updates or features now that sales have started? Thanks a lot!
REPLY ON YOUTUBE
Ugreen have put the NAS’ up for sale on at least their german shop, with a 10% discount. Meaning the DXP4800 is 540€ after discount and the DXP4800 Plus is 720€ , which makes them collide with Terramaster F4-424 and F4-424 Pro. Comparing the Ugreen plus to the F4 pro , i would prefer the more mature Terramaster software , and probably the N305 , over the 4800 Plus ????
REPLY ON YOUTUBE
Anyone else worried about the “custom” Ugreen Linux kernel? This discovery is what made me cancel my order. As someone who works in cyber security, this is very concerning coming from a Chinese company. Please don’t take this the wrong way, there are cyber attacks every day coming from China, and pretty much none coming from Taiwan, where most other NAS companies are based.
REPLY ON YOUTUBE
is there any news on the ugreen nas lineup restocking
REPLY ON YOUTUBE
Can I add full HDD’s with this? Or will it format into raid config?
REPLY ON YOUTUBE
I can’t find a way to sync folders from my ugreen to external usb. Looking I only see rsync nas to nas. Has anyone found a way to back up your folder shares to USB drive?
REPLY ON YOUTUBE
Not available for the uk market?
REPLY ON YOUTUBE
Strange request for a Ugreen NAS video. Showcase how to run Plex using content on an external hard drive. I current am out of space and am using this as a temporary stopgap until I size up.
REPLY ON YOUTUBE
is ugreen nas os linux??? can install jellyfin on that os?
REPLY ON YOUTUBE
BTW, UGreen NAS VM USB passthrough doesn’t work. The option is there but it simply doesn’t work at all.
REPLY ON YOUTUBE
I actually think a video covering how to backup the UGreen UGOS Pro OS would helpful to a lot of UGreen NAS owners looking to migrate away from UGOS but still retain the ability to go back. Also a UGOS image could be useful for running it in a VM.
REPLY ON YOUTUBE
The writing is on the wall for Synology and QNAP. The pace of improvement of UGREEN is very promising. Finally a competitor that’s not trying to sell 5-10 year old hardware like the newest and greatest.
REPLY ON YOUTUBE
Does anyone know if one can reinstall Ugreen native OS after one have installed a 3rd party OS, like TrueNAS?
REPLY ON YOUTUBE
It’s not available yet anywhere. Maybe give it 3 months more???? The hardware is otherwise pretty decent. Can they actually do anything if people just installs TrueNas or Unraid on it instead of the lackluster software it comes with ?
REPLY ON YOUTUBE
Sucks they can’t be found anywhere
REPLY ON YOUTUBE
Could you add a quad this SABRENT 4-Drive NVMe M.2 SSD to PCIe 3.0 x4 Adapter Card [EC-P3X4] SSD PCIe card in DXP8800 Plus?
REPLY ON YOUTUBE
What audio chipset is the nas using
It’s not intel Realtek???
REPLY ON YOUTUBE
Where can these be purchased? I missed out on the kickstarter (cold feet).
REPLY ON YOUTUBE
It is interesting how many people are putting other things on this, basically paying for the hardware.
REPLY ON YOUTUBE
Bought the 8 bay in KS, booted their OS once just to check around, then immediately installed TrueNAS Scale because they don’t have the features I need yet, iSCSI and a few others. Very happy with the system though, 8 16TB HDDs with NVME cache.
REPLY ON YOUTUBE
I bought the 6 Bay / DXP6800, haven’t even opened it yet. Will wait a couple more months before I do to save myself from the first round of bugs / limited OS challenges. I am brand new to NAS and don’t have the comfort level to run / install TrueNAS, UNRAID, etc.. Thanks for the update video!
REPLY ON YOUTUBE
Still not available to buy, and some complaints from people who haven’t yet received their Nas – I can’t see whether that is 1% or 10%, and I think they made it too complicated with that whole discount the $5 reservation fee thingy, and having to fill out forms with address, etc. I’m looking forward to seeing where they expand availability – hint: pick me, pick me, pick the UK. I need iSCSI but I don’t suppose that is in yet. It’s early so we have no idea if the h/w is reliable, but all their other h/w seems very reliable.
REPLY ON YOUTUBE
uh-oh. pink casio video. another banger
REPLY ON YOUTUBE
for only 3 months, this is pretty good progress
REPLY ON YOUTUBE
Do you think UGreen will have a comparable software to synology ? Or will synology still remain supreme
REPLY ON YOUTUBE
Is vadility similar to validity? Hmm…smdh
REPLY ON YOUTUBE
So far almost unusable. New errors are added every day. There are a lot of complaints in the Facebook group and on the Discord. Often the whole raid breaks down and cannot be restored. The support ignores requests. I am currently very unhappy with this.
REPLY ON YOUTUBE
Great summary of the OS so far, I decided to keep using the UGOS instead of using an 3rd party. However, you’ve missed that the connection to active directory doesn’t work and that fine for home users but for homelabs and businesses it’s major oversight.
REPLY ON YOUTUBE
I agree with your review. It’s still beta for the UGOS.
REPLY ON YOUTUBE
I would never use it since I don`t have a use case for a prebuild NAS like this, but if i had one I would be very please with this. Looking at it being their first try on NAS Systems from a company that was not in that business before is quite good and sure, a lot of things aren’t there yet, but as long as the support and development continues, that’s mostly fine with me. I will follow their development and maybe in the future I`ll even recommend them to my friends
REPLY ON YOUTUBE
No snapshots?
REPLY ON YOUTUBE
chinesium software should be avoided at all costs
if I’d buy one of their NASes, I’d put TrueNAS on it immediately
REPLY ON YOUTUBE
It looks like it works well if used as a basic file sharing storage locally
But those promised/soon/will be there/in progress functions seem still not there “yet” ????
There is even no timetable for those things
If just need a basic storage device there are many options in the market
REPLY ON YOUTUBE
Great update video, do wish ugreen had more useful apps. Is it possible u can do a video on how to install tailsacle thru docker on the ugreen NAS?
REPLY ON YOUTUBE
What is the consumption with 6 disks in the ugreen dxp6800?
And temperature?
REPLY ON YOUTUBE
They need to launch in the UK soon! Or I might just bite the bullet and get a Synology 🙂
REPLY ON YOUTUBE
Running proxmox with a truenas VM since day 1, and it’s been perfectly reliable.
REPLY ON YOUTUBE
I picked up the 4 bay “pro” model. I have only used it to host some SMB shares and for those its run flawlessly. I am very happy with it, but my usage is pretty limited.
REPLY ON YOUTUBE
What desktop OS does he run? Is that Fedora Linux?
REPLY ON YOUTUBE
I really need to set mine up its still in box waiting for bugs and other issues to get ironed out
REPLY ON YOUTUBE
Haven’t seen it done yet, but will this run Xpenology? The hardware seems to be a great value, but hearing about shared keys and lack of proper security features worries me. This could be the perfect host for gray-market Synology DSM! And I do realize that’s very much a gray area since DSM isn’t properly open-sourced – though it possibly should be.
But licensing aside, will it run?
REPLY ON YOUTUBE
One of the huge drawbacks is that they override permissions on the homedir every reboot. This makes SSH unusable with keys, only password! I asked the support and got a response that nothing they can do about permission change on the .ssh directory, that’s by design.
REPLY ON YOUTUBE
is the OS outsourced by Synology? it looks too similar in every way I can’t imagine being developed independently and without lawsuits?
REPLY ON YOUTUBE
Is there any official relase date for those NAS Systems?
REPLY ON YOUTUBE
I hate seagulls! But I will admit the YouTube algorithm loves them.
I am waiting to purchase enough drives to fill my 6 bay up, but hopefully soon I can replace two of my Synology NAS with this running TrueNAS. I appreciate your updates on the Ugreen software.
REPLY ON YOUTUBE
I don’t trust them. They added and removed links to NAS from their homepage with no indication of a wider release to the public. I’ll wait for the next Asustor and Qnap offerings
REPLY ON YOUTUBE
Sadly, still not available to buy.
REPLY ON YOUTUBE
Cannot wait for the retail! SSDs are waiting for the lovely 4 bay all ssd nas (and pendrive with unraid)
REPLY ON YOUTUBE
I didn’t even boot into it, I have been running Unraid since I got it and it works flawlessly
REPLY ON YOUTUBE
iSCSI LUN support wouldn’t go amiss either. Support for accessing external (USB and Thunderbolt) storage with MacOS Finder and Windows Explorer (not just through UGOS) is a sorely missed feature.
REPLY ON YOUTUBE
I would have bought one if it were a quiet rack mount solution.
REPLY ON YOUTUBE
Happy owner of a UGREEN NAS, great hardware????!
The software is nice but lacks essential features like encryption and snapshots.
I recommend installing TrueNAS Scale, you don’t need to open the device, and I’ve backed up the original OS on a USB stick.
Zero risk, TrueNAS is 100x better for advances users ????
REPLY ON YOUTUBE
The reality is that the only NAS which is safe is the one which is turned off.
REPLY ON YOUTUBE
“Are NAS Drives Still Safe” depends on how hard you throw them…. ^^
REPLY ON YOUTUBE
Use a router that allows you to isolate all IoT devices on a separate physical network, with its own separate DNS and firewall ruleset–completely apart from the NAS and user workstations.
REPLY ON YOUTUBE
@NASCompares
Isn’t a NAS just an external HDD?
Why’s it opening up computers to so many attacks?
REPLY ON YOUTUBE
If it’s in the cloud, you have no idea, who is accessing your stuff. If it’s in the cloud, then use encryption.
REPLY ON YOUTUBE
VLAN’s! Firewall
REPLY ON YOUTUBE
A google user telling us about security… lol
REPLY ON YOUTUBE
Thanks for the post. Although in IT for over 30 years (retired), I only purchased my first nas 6 months ago- – thus still learning.
I have a Photo/Video business, thus generate a lot of very large projects. I have 2 Synology Nas and replicate snapshots from my production Nas to a backup Nas nightly. On each I have USB a drive and run USB Copy to backup only when I re-attach the drive which is set to eject upon completion. I also periodically skim-off older projects to shelved disk drives. In addition, my backup Nas copies to the cloud. I think I’ve followed all the security recommendations except for port number changes and 2-factor logins – working on these. Does this seem like a good strategy?
My second question is regarding the location of my backup Nas. Besides the obvious advantage of having the backup nas physically offsite, is the nas safer remaining behind my firewall?
REPLY ON YOUTUBE
These attackers aren’t just script kiddies anymore. They can code in their own right. Once a patch is released they will be able to reverse engineer it. In some respects if you don’t patch once the patch is out, you are more vulnerable then you were when the patch was unknown. For Microsoft patch Tuesday, it is known as weaponise Wednesday
REPLY ON YOUTUBE
Thanks for continuing to provide great information. Your commitment is outstanding and the advice very sound. I can’t thank you enough
REPLY ON YOUTUBE
While snapshots and local offline backups on USB drives increase your chances to restore your data after a ransomware attack, they are no 100% guarantee. If the attacker gets enough permissions on your NAS he can delete the snapshots and setup a demon that waits until you connect your offline backup USB drive and immediately wipe it. Never heard of ransomware doing this so far but it is probably only a question of time until we will see this.
The only truly secure backup strategy is to initiate the (versioned) backup from another NAS (or PC) that has as little network connectivity as necessary to do its backups. Like only a VLAN connection to the main NAS that is backuped. That way there is no chance the versioned backups can be deleted or encrypted by any hacked device connected to your main LAN. Agree?
REPLY ON YOUTUBE
REPLY ON YOUTUBE
When you ask are they STILL safe, it implies they are safe in the first place. Hmmmm…..
REPLY ON YOUTUBE
Terrible audio from both of you
REPLY ON YOUTUBE
have been watching hours of your videos on NAS this past week and just want to say thank you for the advice and tips.
I am in the process of replacing a QNAP TS-251 2 bay/4GB that died during the pandemic and have learned so much on what to think about. Its setup in my TV room and is mainly a media storage/player for that room. I did use QNAPcloud previously but am going to shy away from it being on the net for the initial stages of use. Its a 1080p room and for the most part use.264 files. Is there a NAS you would recommend for my purposes if I am wanting to stick with QNAP or Synology? THe local computer store is saying that I should stick with QNAP and the data on my previous 10TB can be saved as it will not be formatted for new QNAP enclosure. I am not sure that is should just plug those drives into the new enclosure in case there are vulnerabilities or applications that will cause me grief. Any thoughts would be appreciatted.
Again great stuff and sorry for the long post
REPLY ON YOUTUBE
Conclusion: There’s no bullet-proof way to setup a set-and-forget NAS connected to the Internet? ????The safest 3-2-1 backup configuration would probably be an intranet with the “offsite” NAS being located in the building next door, am I right?
– Eero
REPLY ON YOUTUBE
Great information thank you very much for your services of much-needed points for us the end users of NAS products.
REPLY ON YOUTUBE
If you were using a QNAP and did not want to set up a VPN, Qlink allows remote access with no port forwarding. And without port forwarding, the NAS is a lot more secure. Qlink is very easy to use.
https://www.qnap.com/en-us/software/myqnapcloud
All other myqnapcloud features besides Qlink can be turned off for higher security.
Once Qlink is set up, you can send share links to files or folders using the SmartShare feature.
As for file transfers, Qlink will let you do that from the GUI. But QNAP also supports Resilio Sync to sync folders with PC or Mac with QNAP. And that works without port forwarding.
I would still consider VPN to be the best option for remote access. But qlink and Reslilo are so easy to use that I think it should only rarely be necessary to forward the https, FTP, ssh, or rsync ports.
REPLY ON YOUTUBE
Minor edit, the links in the description is wrong
Previous NAS Safety Videos:
Is Synology NAS Safe? – points to QNAP! – https://youtu.be/o29KFsECQzc
Is QNAP NAS Safe? – points to Synology! – https://youtu.be/oHrry2i9b1o
REPLY ON YOUTUBE
Definitely QNAP isn’t.
REPLY ON YOUTUBE
Offline backup that is offsite just incase my house burns down…
REPLY ON YOUTUBE
Yes, the sound quality on this one is quite rough, isn’t it! This video was one of THREE that were recorded between me and Eddie, only to discover that OBS has double sync’d my mic and camera – the result is one of the BASS’iest sound levels I have ever recorded. We are in the process of re-recording the other two videos, but this one was moderately salvageable. Much like in a previous video, trying to sync mine and Eddie’s sound proved 10x harder than it should have been and in the end the balance of the audio was leveraged more towards Eddie (as I am always the louder/noisier/more-annoying one!). Sorry if this makes it tough to listen to at points. Have a great weekend everyone! Might have to revisit this one, just seemed a shame to throw it away, as 2nd record will be too scripted/repeated. Hope you all understand. Have a great week ladies and gents!
REPLY ON YOUTUBE