Are NAS Drives Safe Enough to Use in 2024?
Are you a NAS owner? Perhaps you are considering buying a NAS based on a recommendation from a friend, work colleague, IT professional or even myself (Robbie) on YouTube. The appeal of owning your own server, cutting the connection with your subscription cloud providers such as Dropbox or Google drive, having all your data backed up in-house and that feeling of pure control/ownership is hard to underestimate. However, over the last 4-5 years or more, it has been hard to ignore that the brand has suffered a series of security issues surrounding the subject of ransomware – a process whereby your data is encrypted with a unique, near uncrackable cypher and a document (typically a .txt) is left for you with instructions for you to make a payment in bitcoin to a predesignated account in order for instructions and the key to recovery your data. Ransomware in of itself is not new and originally dates back to 1996 under the name cryptoviral extortion (you didn’t come here for a history lesson, but the wiki covers a lot of those early developments into the concept) and is frighteningly easy to conduct IF an intruder has access to your system and/or the means to inject the command to encrypt the data inside of any system. Words like virus, hack and malware have been thrown around the internet for the last 20-30 years, however, Malware feels significantly more organized and comparatively recent, as well as being something that has been enacted on all storage platforms, such as Google Drive (thanks to sync tools), Apple was directly hit in 2021 and over 300 BIG name companies that you WILL of heard of in the last 18 months that included:
Acer, FujiFilm, Northern UK Rail, Exabyte Web Hosting, Foxtons, The Salvation Army, Shutterfly Photography, Bose Sound, The NRA, Kronos CRM systems, Gigabyte Motherboards, Volvo, SPAR, Olympus Cameras, GUESS Fashion, ADATA, CD Projekt, Travelex, SK Hynix, Capcom, Crytek, Kmart
Those are just a brief scan of confirmed news reports and only a small fraction of the companies, brands and institutions that have been successfully targetted. Tech companies, media companies, charities and countless retail outlets. Why am I going through all this? Well, 1, these companies should have exceptionally sophisticated storage and remote access protocols in place, 2, cannot use the excuse of being companies with practically no formal association with high-level storage and 3, are companies with a responsibility to protect significantly custom databases that eventually fell foul (partially or fully) to vulnerabilities. Personally, I DO think, when NAS brands have blame on their side (eg Asustor/Terramaster with Deadbolt, QNAP with QLocker, Synology with SynoLocker, etc) that they need to acknowledge publically, make significant errors in these attack proactive management AND have handled a number of the follow-up actions to these incidents very poorly (both in terms of communication and execution) – They need to put their hands up and say “We F’d Up” and take responsibility, up to a point! However, I do also think that the end-user base is also not completely innocent and alongside ascertaining whether any particular NAS brand is safe to use in 2024, we should also think about how we store data, the limits of our own due diligence and our expectations from server devices.
Important note – If you are currently unaware of the severity of ransomware attacks, malware attacks and authentication bypass vulnerabilities, you need to subscribe to this page HERE on NASCompares. Also, if yo are in any doubt about NAS security and owning a system, REMEMBER, the very LEAST you can do is:
- Set your system software updates to automatic (either FULL or just security updates)
- Disable the ‘admin’ account (it should be disabled by default, but make sure!)
- Disable SSH / Terminal services if you are not using them (again, these should be ‘off’ by default, but check)
- Create exclusre login credentials to services/clients (eg Plex should/can have a user:plex + password, and then restrict that account to only the folders and services that it needs, then restrict or ‘ready only’ the rest
- Have at least one backup in place. Remember that a backup is a complete copy of all your data in a different system/location!!!
- Change random ports in the system for accessing the NAS (you tend to find NAS systems use 8000, 8001, 8080, 5000, etc. Change them to something random)
- Enable 2 Step Authentication / 2FA / OTP
- Do not F&*k around with your router or open ports unless you know what you are doing!
Additionally, if you have been affected by ransomware on your storage solution (QNAP, Synology, UnRAID or whatever brand), this post is not intended to play ‘blame games’ or detract from the impact (personally or professionally) that it has caused. I have experienced ransomware attacks, malware attacks through my browser, virus attacks on my OS and seen my fair share of attacks fail and (annoying) succeed. Please do not take this article in the spirit of ‘get stuffed, It’s your fault!”, but as a means of dissecting the current state of play with NAS devices and the realistic expectations/responsibilities of all involved.

PSA – GET YOUR BACKUPS IN ORDER!
Before you even go one paragraph further, I have a simple question for you – do you have a backup in place? If yes, then carry on to the next part. If not, and I cannot stress this enough, GET ONE NOW. The time you are spending reading this you could be susceptible to data loss in about 10 different ways without even factoring in ransomware (Power failure leading to hard drive corruption, Malware from a slightly iffy google search this morning, cloud storage provider going bust, OS failure on your device, etc). In this day and age owning a sufficient data backup is as sensible as buying a raincoat or looking both ways when you cross the street – you don’t do it because you like rain or like looking at cars, you do it because they are peace of mind, they are a safety net, they are for caution in case of the worst. It is a bit tenuous, but owning one or multiple backups always make me think of this quote from Shawshank Redemption by Stephen King:
“There are really only two types of men in the world when it comes to bad trouble,” Andy said, cupping a match between his hands and lighting a cigarette. “Suppose there was a house full of rare paintings and sculptures and fine old antiques, Red? And suppose the guy who owned the house heard that there was a monster of a hurricane headed right at it. One of those two kinds of men just hopes for the best. The hurricane will change course, he says to himself. No right-thinking hurricane would ever dare wipe out all these Rembrandts, my two Degas horses, my Jackson Pollocks and my Paul Klees. Furthermore, God wouldn’t allow it. And if worst comes to worst, they’re insured. That’s one sort of man. The other sort just assumes that hurricane is going to tear right through the middle of his house. If the weather bureau says the hurricane just changed course, this guy assumes it’ll change back in order to put his house on ground zero again. This second type of guy knows there’s no harm in hoping for the best as long as you’re prepared for the worst.”
Get a Backup in place
More Ransomware Attacks on QNAP than Any other NAS Brand?
WannaCry, QLocker, eChoraix, Deadbolt, how, many, times…

Probably the most compelling argument against the safety of NAS for many buyers is the simple fact that NAS brands increasingly seem to been in the news more for reasons of ransomware attacks. Indeed, even a quick browse of the last 24 months on the site ‘Bleeping Computer’ for stories on QNAP shows you that there have been multiple vulnerabilities found in their software/access that have allowed encryption commands to be injected into the QNAP NAS system to execute the ransomware attacks. How can this one brand be such a soft target? What are they doing wrong? Well as it stands, reading through news posts before/after previous ransomware attacks, as well as the dissection of events on the official forums in the midst of the an attack, the consistent threads are:
- QNAP is rolling out software and services with weak default settings and acceptable minimums to allow inexperienced users to open up external access WITHOUT the users understanding the risks
- QNAP has weaknesses in it’s software that the brand arguably takes a more reactive, than proactive stance on repairing
- QNAP’s recommendations on actions to user post-ransomware attack both publically and in 1-to-1 dialogue with users has been felt unsatisfactory
- Your QNAP NAS is better off currently used offline/network only
As general as all that might sound (without letting personal opinions colour it) those are largely the four core issues for many that have voiced their feelings on this in the forums. Moving away from the hefty subject of data loss slightly (we will be returning to that in a bit, but that is a question of Backups and routines to discuss), there is the fact that there have been vulnerabilities found in QNAP 1st party applications and services – but then again, so have there been in different NAS brand’s own services too. A click look at their respective Security Advisory pages will tell you this. This doesn’t exonerate QNAP in any way here, as part of the ‘social agreement’ between the end-user and QNAP is that as long as we ‘follow due diligence in protecting the data inside the NAS as directed AND maintain our own network/router setup, the QNAP NAS should protect our data inside the NAS to the best of it’s ability. This is where it all becomes problematic. As QNAP have never successfully balanced the line between giving the user freedom, control and customization WHILST still preventing the user from doing anything self-harming without a full idea of the consequences. It’s a line that their biggest competitor Synology seems to toe better and this comparison only serves to re-enforce the feeling (and numbers) that QNAP are attacked more.
The Nature and Practice of Firmware Updates on ALL NAS Brand Devices – Prevention & Cures
“Remind me Tomorrow” click
Though sometimes NOT the means with which a vulnerability in the NAS software/services is achieved, it is still a factor in some instances that updating to a later firmware would actually have closed a vulnerability. However, this is a remarkably broad statement and the truth is a great deal more nuanced. First, we have to understand that ALL software that has a remote access component via the internet will likely be investigated by cybercriminals for weaknesses. Not just NAS ones – ALL of them, from Microsoft office and Android mobile OS, to your LG TV and Amazon FireTV. Hell, I bet there are people who have investigated the ‘buy now’ option of WINRAR in effort to see if an opening exists to use it as a ransomware entry vector. What I am saying is that as soon as a commercially popular software with internet access exists, people are going to try and take it apart to find out its weaknesses for exploitation. If/When these weaknesses are found and actioned (or submitted to the brand for bounty programs – whereupon brands ask people to try and break their software, so they can make it better/safer/improved), the brand then issues a firmware update to the affected software/services to its user base, then around the merry-go-round we go again! This is not a process that happens daily – but it definitely happens weekly or monthly (depending on the frequency of the brand to instigate the changes that are raised to them). This is why is it so common for companies that are affected by ransomware in their software/services to immediately highlight the need for firmware updates. At that point, the attack vector and vulnerability is reverse engineered, patched and closed. Many of these vulnerabilities are small. Very, VERY small sometimes. Indeed, it is for this reason that all the reputable NAS brands have security advisory pages that list current weaknesses, vulnerabilities and issues on their platform that are being investigated (Synology HERE, Asustor HERE and yes, QNAP HERE) and in all my time in the world of network-attached storage, I do not think I have ever seen one of these pages have ‘100% resolved’, but when something is resolved the resolution is invariably rolled into an update. So what we can take from this is that although firmware updates do not completely remove the possibility of new vulnerabilities being found in the future, they do seemingly close the bulk of existing vulnerabilities that have been found by/volunteered to the brand.
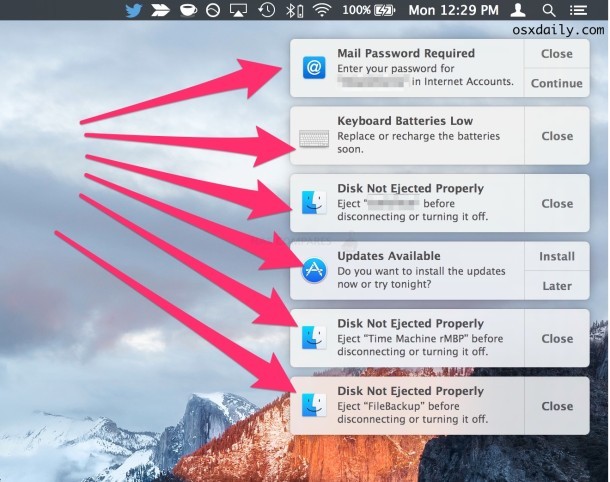
So why do we not install the firmware updates automatically? This isn’t limited to NAS of course! From the Mac notification that have been nagging you at the top right of your screen, to the windows update at the bottom right and all those applications on your phone that are asking you to please install the latest updates to your software – we choose to ignore them til ‘later’! Worse still, there is the old ‘if it ain’t broke, don’t fix it’ mentality that will often result in many users only installing smaller updates, but flat out avoiding the BIG updates as they can ‘change where everything is’ or ‘I heard it breaks a bunch of stuff’. Businesses in particular with shared files in their thousands are always reluctant to run any process that can suspend that access temporarily or change how something works. So, there we have a fine melting pop of ingredients that has led (in some instances, but not all – as we will go further go into) to many users being hit by ransomware attacks via vulnerabilities that, although patches were available, were not actioned. How do we resolve this? Forced update that leaves the user’s own hesitance out of the equation? Limitations of the system’s remote connectivity unless the latest firmware update is installed (console gamers will be very familiar with that method of course)? Or a 50/50 split where minor updates are optional, but larger ones are mandatory? It’s a tough tight rope to walk. So, let’s see how QNAP walked/walks this tight rope and how they could have possibly done it ALOT better.
System Updates and Updates – Should a NAS Brand FORCE Firmware Updates to Users?
Forced? Optional? Access Penalties?
As mentioned, tighter control of firmware implementation would allow the brand to ensure that a NAS that has internet accessibility is updated to a high/current firmware revision. Alternatively, the brand could limit the systems external connectivity and disable all settings if the firmware on the system is not up to date – simply running a check with the NAS brand connected domain when trying to access these services and settings and declining if the latest update is not installed. Xbox and Playstation users are more than aware of this as a fixed rule to ensure that installed software is officially licenced and checked in advance. However, those are closed systems and many buyers have selected NAS over cloud services precisely because of the flexibility and customization it offers. However, when NAS brands have previously FORCED firmware updates remotely for services, it has NOT been received well:
Forced updates are something of a taboo subject too, with the recent rather heavy-handed move by QNAP back in 2020 in light of the Deadbolt ransomware attack to remote push the latest firmware update to all QNAP NAS systems that were internet-connected without any notice to the end-users (overriding any settings that disabled or prevented this). Now, clearly, QNAP did this as an extreme and something to prevent the vulnerability of the system software and/or configuration from being exploited further (that have still not been fully confirmed in its attack vectors, with some users who have ridiculously high-security settings still getting hit). In non-ransomware instances, I think QNAP issuing a message to their user base with a “In 5 day’s there will be an essential system update on XX day XX month at XX:XX time” message, with even a brief explanation of why would have been infinitely more preferable and would have been met with a much more positive stance (as well as it also making many users update sooner). However, clearly, the decision for a forced update was more of a last resort/hastily decided choice and that forms part of another reason that many users find the QNAP platform to sometimes bring services and software to market that could do with a little more time in the oven. Whatever way you look at it, QNAP was going to be damned, whatever they did. But did they put themselves in this position? What about the expectations of the end-user and due diligence? What SHOULD be the expected skillset of a NAS buyer to start with?
The Extent of the End User Responsibility, Skillsets and Expectations? What Are YOUR Responsibilities as a NAS Owner?
How much should a user be expected to know about networking?
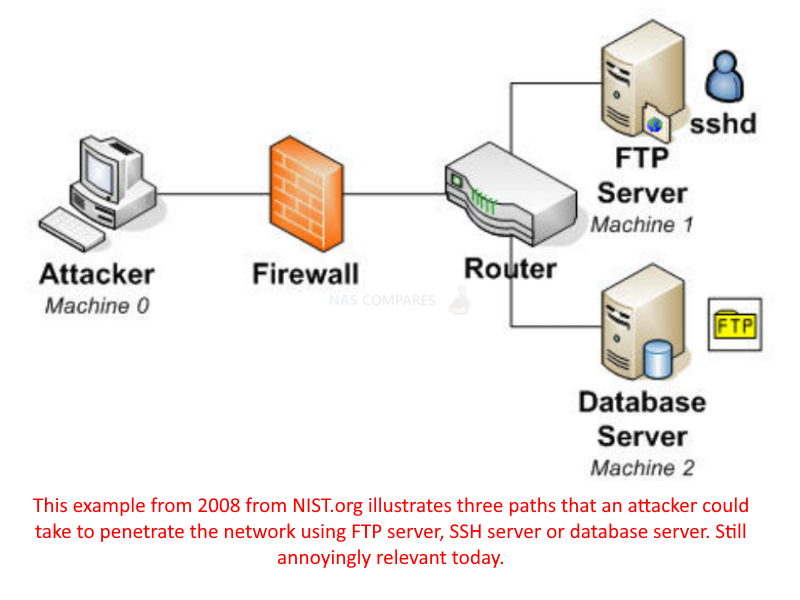
The simplicity of NAS systems can often be oversold. It’s annoying and I am as guilty as most of this, but given the wide range of users who install a NAS system into their storage environments, the ease of setup and use is not shared with the ease of setup and understanding of network security in your home or office. On the one hand, NAS brands have supplied multiple services and processes in their system software that make remote access easy, encrypted transmissions easy, SSL certificate applying easy, 2-step authentication easy, UPNP and router pushing easy – you name it, they have tried to make it easy. But should they have? The ease of setting up a number of these services (as well as non-randomized settings in some places) can easily give users a false sense of security. So, for those users of a higher skillset, it would be acceptable that a NAS should only be remotely accessed with the highest layers of security applied, and it should not allow remote level access to be possible without some unique intervention and set-up by the end-user (not just a password and/or disabling an admin account), although to stop presets of this nature would lead to a noticeable spike in the difficulty of setup, perhaps that is what is needed. This is by no means a new issue we are discussing and even a brief google search online finds examples of attack vectors and methods as far back as 1999 on public/org sites.
However, in reality, it simply would not work like this, The user base of most established NAS brands are just too varied and though these tougher and more unique security implementations would secure things, the less technically skilled users would hit hurdle after hurdle, once again, one of the prices of some (not all) of that flexibility. Alot of users who have been hit by ransomware attacks have specifically headed to official forums because they do not have the remote setup experience that might be deemed an acceptable minimum to start opening ports via the NAS settings or directly on the router. This once again brings us back around to what should be the expected skill level of an average NAS Drive owner, how much of the control and security profile of the storage system belongs to the NAS manufacturer and how much should the buyer be expected to do independently? You can buy a car, you can fill it with petrol and the manufacturer can tell you its top speed, and miles to the gallon – but no car manufacturer would feel the need to add to all their adverts “must have a driving licence”, do they? It’s a rather stretched simile I know, but the fact remains that users cannot expect to connect their storage to the internet in 2024, open up pathways to it via the internet and not at least make allowances or provisions that an attack could happen. This leads us to the hardest and coldest fact of practically EVERY SINGLE NAS related recent ransomware attacks that, although only applies to a % of users, is still depressingly true.
How Backups and Data Storage are Still being Misunderstood – UNDERSTANDING WHAT A BACKUP IS, AND A NAS IS NOT!
A frighteningly large number of victims with no backup. Acceptable backup levels?
One of the hardest choices for anyone that has been successfully targetted by ransomware attackers (not exclusive to NAS either) is the choice to pay or not. When I am asked to make recommendations for a home or business user in the free advice section here on NASCompares or the comments on YouTube, I will always ask what the user storage quote is currently (now then double annually over 5yrs), their user base (volume and frequency) and their budget? That last one is always a kicker for some, as no one wants to show their cards! I’m not a salesman and I do not work for a eRetailer, I ask because there is a lot of ground between a £99 DS120j and a £5000 RS3621XS+. However, budget is INCREDIBLY important and should not only be measured by the number of 0’s in the account, but also by the cost of if the data is lost! Many users are so busy thinking of how much it will cost to provision for the future, that they are not factoring in the cost of replacing the past! This is the exact personal vulnerability that ransomware targets and sadly, a lot of users still do not understand 1) what a backup actually IS and 2) what a backup actually ISN’T.
If your data ONLY lives on the NAS, then the NAS is not a backup. You likely knew that. But socially and conventionally, we tend to forget it quite easily. We make space on phones by deleting stuff because ‘it is backed up on the NAS’. We sync our laptops and MacBooks with a remote folder to keep our files safe on the NAS, but still make changes or delete files on the hoof. We take the NAS as red as a backup and at that point, it isn’t! Likewise there are things that SOUND like backups… RAID… Snapshots… Hot Spares… they sound very reassuring, but are not backups, they are safety nets! And are all typically found ‘in system’. A REAL backup is something that is the same files, ELSEWHERE! There is no avoiding that a NAS (Synology, QNAP, TrueNAS, Whatever!) is NOT a backup solution in of itself, but can be used IN a Backup Strategy. All brands highlight at numerous points on their website that you should have a 1-2-3 Backup strategy, or a bare-metal and cloud backup, or a periodic USB backup, a NAS to NAS remote backup – or ALL of them! Sadly, there are a lot of users in the official NAS branded forums that have been hit by ransomware and did not have backups in place, with some knowledge that they needed a backup but their budget’s prohibited it. Whilst others say that a NAS brand publishes in its online literature that it’s a backup device, they bought it as a backup device, therefore the company missold it and that is the end of argument!
The sad truth is that the brand is not responsible for your backup routine or strategy, it supplies the means to store and access data and their responsibility (succeed or fail) is to ensure its hardware and/or software provides a default secure level of access, as well as the means to configure that access to the users control. There HAVE been vulnerabilities found and they have patched them, as is the usual process in these things (at least, they say they have at that is the best guarantee we can ever have from a brand in the circumstances), but they are NOT responsible for your backup routine. This now leads us to the subject of the NAS hardware, the NAS software and comparisons between brands.
Hardware vs Software Priorities – Is Synology Safer Than QNAP?
Hardware vs Software, QNAP vs Synology, Is the grass greener?
Way back in the mid twenty-teens, whenever I would discuss QNAP and Synology on the platform, I would always say that you go to Synology for the Software and QNAP for the Hardware. Synology’s DSM platform clearly makes up the bulk of the companies investment and attention, makes up a significant chunk of the price tag and is designed around keeping things as user-friendly as possible (within reason). This is why their devices at each generation refresh (DS918+>DS912+>DS923+ or DS218+>DS220+>DS224+) only make smaller increases on the previous generation – the software IS the focus. With QNAP we tend to see the hardware taking bigger leaps each generation. Better standard ethernet, better PCIe gens, Better CPUs much earlier and overall greater hardware at any given time. For PC builders and those that know a lot more about the contents of their laptop than the contents of their router, this is speaking THEIR language and makes the price tag translate better. Fast forward to now and although that logic still remains the same, these brands are more 60/40 in their architecture (where 60 = their preferred hardware or software bias). The issue starts when QNAP seem to rush their software out the door very quickly. Alongside a lot of more beta applications being available, they roll out a lot of new types of software that (and I am sorry to use that expression again, but) could have used more time in the oven. This approach to software development and release can be dicey and although it makes QNAP the more exciting platform (with its better hardware, more diverse software and continued AI or generally automated services), it also means that the platform has less of the layers of troubleshooting red-tape that Synology has (which inversely means the Synology product is going to be more expensive and less hardware rich, as that investment of time needs to be repaid to be justified). In recent years, QNAP has seemingly slowed down it’s hardware releases and rolled out more in software, introducing bounty programs for vulnerabilities, pen testing and is seemingly learning from their mistakes (we hope). Whilst Synology have further doubled down on software innovation, with solutions remaining longer in the market between refreshes) and continued on their path to continued dominance in NAS. Whether you look at the whole thing as a tortoise and the hare situation, or a case of ‘slow and steady wins the race’, there is no denying that Synology appears to take security more seriously than most other brands.
Look at the Apple TV box or Amazon FireTV / Firestick? Is it user-friendly? yes! Is it slick and intuitive? Yes! Is it flexible in the installation of 3rd party applications? NO (at least, not without workarounds)! Is it hardware-powerful? LORD NO! One glance on eBay will show you a thousand other media boxes at the same price with Android on board, 5-10x the hardware and customization coming out of the wazoo. Nevertheless, many users will not buy the apple/amazon media option because although they KNOW it will be slick and ‘hold your hand’ all the way, it will be a closed system, noticeably more expensive and even then “nothing is full proof, right?”. And a lot of the anger at QNAP for their increased ransomware targeting and handling of this needs to also be balanced against why a lot of users chose the QNAP NAS brand. The QNAP NAS platform does have good applications and services, some genuinely unique ones and ones that allow tremendous flexibility and customization – but users need to remain relative to what drew them to the platform and have sufficient backups AND safety nets in place. I would say this about QNAP, about Synology, hell… Google drive, DropBox, Backblaze… ALL of them have localized client tools that rely way too much on the success of versioning/roll-backs being possible on the cloud platform. None of them are 100% full proof and QNAP dropped the ball multiple times here, but none of these ways are unprecedented and should be provisioned for regardless of your NAS brand or cloud platform.
The Sad Truth about Servers, Security and Vulnerabilities
Vulnerability > Update > vulnerability > update > rinse > repeat
No platform, software or service is going to be 100% bulletproof. You can increase your personal layers of security (VPNs, Encryption, layers, restrictive white lists, etc) to hit 99.99% but whatever way you are looking at it, everything we use is software-based and therefore, fallible. Equally, users cannot pretend that it is still the early days of the internet anymore and still be annoyed when a statistical possibility that should have been factored against was not. Do I think NAS drives are safe? I’m sorry to say that the answer is never going to be a simple Yes/No. I think they provide what they say they provide and I think that NAS hardware is still the best in the market right now. But the majority of NAS brand software needs to be less rushed (I somewhat absolve Synology of this, as they seemingly take it 10/10 seriously!), the extra time/budget be spent on that software, or utilize a trusted 3rd party. The need to relinquish some of the customization of their platform in efforts to remove some of the configuration out of the hands of less tech-savvy users who end up overly reliant in defaults. Perhaps a much more rigorous setup policy that, on day 1, have an EXPERT door and a NOVICE door, with randomized defaults and extremely regimented update rules on the latter. Equally, the brand (though better than it was) needs to work on its communication with its end-user base, both in the event of critical issues and education on what the user base needs to have to increase security OUTSIDE of their product.
I still recommend the majority of turnkey NAS brands in the market in terms of their bse product and the range of security/system protection tools they include, but we need to be realistic and honest with ourselves about what we buy and our expectations. If I buy a NAS, I expect it to store the data I store in it and allow me access to it on my terms, but ‘my terms’ might be a lot more/less strict than the next person and with that comes due diligence in 2024. I hope that the last big ransomware attack, deadbolt from the start of 2022, is the last ‘big’ one we hear about moving forward, but I do not think it will be. More than just any one brand, one look at the vulnerabilities listed on security advisories of all the brands tell us that there is big money to be made by these intruders and the brands can only stay 1 step ahead. As always, me and Eddie here on NASCompares have been running a page that links to the bigger NAS security Advisory pages that gets regularly updated, so if you want to get notifications on these as they get added (pulled from the official pages themselves), then you can visit the page below and put your email in for updates when they happen. Have a great week and backup, backup, BACKUP.
Click Below to Read
Finally, If you are currently unaware of the Deadbolt ransomware attack that took place on QNAP NAS devices, you can find out more in the NASCompares article and video below:
 |
📧 SUBSCRIBE TO OUR NEWSLETTER 🔔
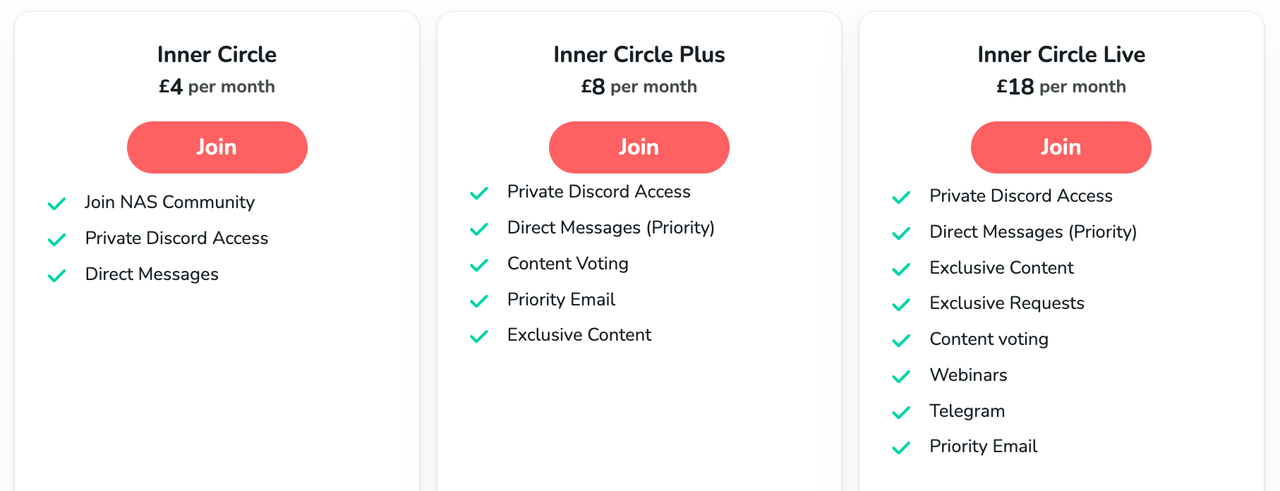
🔒 Join Inner Circle
Get an alert every time something gets added to this specific article!
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.

|
 |
WHERE IS SYNOLOGY DSM 8? and DO YOU CARE? (RAID Room)
UniFi Routers vs OpenWRT DIY Routers - Which Should You Choose?
WHY IS PLEX A BIT S#!t NOW? IS 2026 JELLYFIN TIME? (RAID Room)
Synology FS200T NAS is STILL COMING... But... WHY?
Gl.iNet vs UniFi Travel Routers - Which Should You Buy?
UnifyDrive UP6 Mobile NAS Review
Access content via Patreon or KO-FI
Discover more from NAS Compares
Subscribe to get the latest posts sent to your email.




I was hit by deadbolt ransomeware some weeks ago. Finally I got the key and my files have been fully decrypted. Thank you
REPLY ON YOUTUBE
I remember the same attack done at Synology, ransomware attack demanding 1.2 bitcoin, unfortunately I paid them and they gave the key and I unlocked all of my 10 years worth of files .
since then I unplugged my NAS from internet and don’t use its feature.
what synology did? they sent me $30 headphone… imagine that, I paid 1.2 bitcoin for cheap headphone.
I was considering Qnap until I find this video
REPLY ON YOUTUBE
No.
REPLY ON YOUTUBE
QNAP the most attacked NAS on the planet and worst support. I lost 7tb of data with no way to recover.
REPLY ON YOUTUBE
I have secured my QNAP and it has been safe until Saturday when I got hit by Deadbolt, but my most recent snapshot come to the rescue……the thing is that my QNAP was secured as far as I was aware…..????????????????????????????
REPLY ON YOUTUBE
I am IT consultant for 20 years and i loved to had the opportunity to watch this video. To me the thing that QnAP does not have any guilt in their product its at least a bit biased. I know people want to sell NAS and make a good chunk of commissions, its how things works i got that.
But lets face it with a great example, if you have a Tesla, are driving and the car crushes because the system does not allow you to stop, then even if there is a bug there, the brand is responsible, not the end-user for sure.
When we translate the NAS issues, well sure , the end-user needs to have a specific skill set to be able to know how to work with the technologies, but the brand does not say its it can be challenging for some people, who does not understands, a,b,c… etc…. Instead they tell you that you can have everything setup by clicking a simple button, and the more features it has the more people will activate.
I never saw a disclaimer from QNAP or any other NAS brands about what can happen if the users does not have that skillset, and even worst, they market it as a product that is top notch in technology, like having access to the nas content from everywhere. That´s where they have responsibility, i am quite sure some lawsuits will occur sooner then later.
Because they have the responsibility to explain clearly what a basic user should do and should not do…
They also should explain that someone before buying a NAS should have at least a 3-2-1 backup solution , because the NAS is not the backup solution.
I know that for many people, the NAS itself its quite expensive to buy and so many users cant afford to buy external drives for Local backups and also a cloud backup system, that is the bare minimum for whom thinks about having a NAS as home or in a SOHO
And here again i never seen QNAP explaining in a very clear way in their sale pages about their NAS products, when i am talking about QNAP, its not only QNAP , other brands do the same, but are they responsible brands by doing so? in my honest opinion nope.
Probably many small business went out business, some because ethically they don’t want to pay to criminals and others because they cant afford to pay due to the crisis that have impacted so many people worldwide.
Here i believe that QNAP should paid the ransom to solve this issue for their customers, are they obliged to? of course not, but in the other hand they would not have their image burned out and their online reputation is not good to say the least.
I have a QNAP nas devices and i am quite sure that i will never ever buy another from this brand again.
REPLY ON YOUTUBE
I think every brand should add a choice at setup that asks, what is your data classification: very private, private, public. And what is your update tier: beta, innovative, stable and secure. From that the system can make the appropriate choices.
REPLY ON YOUTUBE
he did the job for me even when it seemed????????
not possible thank you very much.
Translate to????????????
REPLY ON YOUTUBE
* 4 months August @ I really appreciate you for the professional work you do to get my cell phone back you are the best I recommend it @ ☝️☝️☝️☝️☝️
REPLY ON YOUTUBE
Worker with a reliable hacker is what I think is all over the world and I recommend a hacker parfait who works with good heart and sincerity Dee_hack11 is in Seoul☝️☝️☝️.
REPLY ON YOUTUBE
Worker with a reliable hacker is what I think is all over the world and I recommend a hacker parfait who works with good heart and sincerity Dee_hack11 is in Seoul☝️☝️☝️
REPLY ON YOUTUBE
????????????????????Contact this hacker he is honest he helped me recovered my files I’m grateful
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now.
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now
REPLY ON YOUTUBE
After trying for some time, I had to contact *SCOTTS_HACK* to help me get the deadbolt off my Nas. I’m free now
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
*I was hit, so unplugged, shutdown, external USB backs fine. Plex user, was watching at the time no issues, went to update saver denied, then found the splash screen, no on reboot, water gapped on an independent switch no WiFi etc, it instantly goes to initialization. So save to assume the service themselves have been affected. Did safe shutdown. After some time I turn on everything then I found out I’ve been truly hit by deadbolt. I did as many research as I could and I found out that scott can actually decrypt the encrypted files. So I paid some money not upto what deadbolt team are asking, then he decrypted my files*
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you.
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you
REPLY ON YOUTUBE
Good day all, for DEADBOLT RANSOMWARE REMOVAL, consult *SCOTTS_HACK* Thank you
REPLY ON YOUTUBE
.You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
.You can message *SCOTTS_HACK*
REPLY ON YOUTUBE
Am cool with #GLOCYBER idea. He has much research on the virus and has helped a lot including my self.
REPLY ON YOUTUBE
Am cool with #GLOCYBER idea. He has much research on the virus and has helped a lot including my self.
REPLY ON YOUTUBE
????I was so glad when I finally realized and get in touch with Glo Cyber while I used the contact above. He is indeed a genius and his skill are authentic. I rec. everyone to appreciate his efforts.
REPLY ON YOUTUBE
People keep talking about Scott. I think he is good. I will try him.
REPLY ON YOUTUBE
Someone recommended you ????and you also helped me recover mine too. You a genius indeed.
REPLY ON YOUTUBE
Let Eddie say something…
REPLY ON YOUTUBE
I wouldn’t touch QNap with a barge pole until they drastically change their approaches to the user base, contempt for the user base isn’t a great strategy.
REPLY ON YOUTUBE
just got hit and i was on latest firmware and all apps updated
REPLY ON YOUTUBE
You’re ???? such a genius, I really appreciate your services, fast and safe recovery process..
REPLY ON YOUTUBE
You’re ???? such a genius, I really appreciate your services, fast and safe recovery process..
REPLY ON YOUTUBE
My QNAP NAS used UPnP to open all of the ports needed for bad actors to try brute forcing their way in. I was getting over 1200 login attempts per hour.
REPLY ON YOUTUBE
I think forced updates should be a requirement for utilizing certain features. So, if I enable remote access through a firewall of any sort, forced updates should be enabled. IT enabled organizations wouldn’t be making use if these features anyway and in can absorb the risk of automatic/manual updating.
REPLY ON YOUTUBE
I think they get attacked because they move into Face/Facial/Eye/Mask screening. People don’t like that. This is a threat to privacy. I think that is the root cause of it. I don’t know if Synology is in the same as such.
REPLY ON YOUTUBE
I regret I have missed this video 2 weeks ago. #asustor #deadbolt
REPLY ON YOUTUBE
I’m sorry I purchased a NAS as a means to have a BACKUP of what is/was on my laptop or pc. And it’s even sold as a backup. It started with ‘consumers’ being told to connect an external hard drive to backup their data. They would even supply at times backup software. So you backed up to this external drive. Then they started to sell NAS which was a way to still Backup and be able to access those backed up files from any connected computer.
So I disagree that you cannot thing of the NAS as a Backup.
Evidence: Why do they supply NetBak. Which can backup or copy your PC to the NAS.
So if you say the NAS is not a Backup tell these companies to stop supplying backup software that works to copy to these systems.
When I was told I needed a Backup I bit the bullet and purchased a second NAS which is used only to receive a Backup Data from the Main NAS! Its stupid but I understand it.
Especially since this last issue I had to erase my partitions to fix my issue. Great!
REPLY ON YOUTUBE
Wow I liked how you pointed out tech support being abrupt.
I reported a problem months and months ago and it was just impossible to arrange for remote support.
Then there was an update which fixed the problem we were trying to work on. So I basically wasted tons of time trying to recreate the problem and pin pointing the actual issue.
So why was I spinning my wheels for months when they knew about the issue.
Just tell me and ask me to be patient while they fix the bug. Why make me waste my important time for this sh*t.
I also had a problem of the NAS running so slow I could not even log in via the web. Thankfully I have a unit that has a hdmi port and was able access it via direct. But still could not use the system.
That was months and months. I was planning on dumping the whole thing. But it meant dumping two QNAP units. The cheaper of the two worked perfectly. I was angry.
Then I read something in a forum and decided to try it. I had to stop running Q’Center. Once I turned it off and removed it my system ran normally.
The same thing happens when you run McAfee. Of all things to slow down your unit so its unusable what is the purpose of having anti-virus. And whomever says its not needed needs their hand examined. You do!
The built-in anti-virus finds things that McAfee does not? And yes they could be false flags but it works.
REPLY ON YOUTUBE
Great video! I just saw lex friedman video and he talks about his devastating qnap ransom attack.
REPLY ON YOUTUBE
your videos could be a bit shorter and more concise. Lots of filler that doesn’t give a lot of information.
REPLY ON YOUTUBE
Not an IT expert but I bought an entry level Qnap NAS, which is now not connected to the internet and I’ve manually updated. What I’d really like to see is a guide to setting the NAS up safely so that the NAS is available to the home users, but protected from the internet outside. Backing up to two USB drives BTW!
REPLY ON YOUTUBE
Great discussion, can an OpenVPN / windows vpn on QNAP do it? and not juse myQNAPcloud? can it not be a good option? between one’s server and user outside of one’s network.
REPLY ON YOUTUBE
OpenVPN / windows vpn on a QNAP , and not juse myQNAPcloud?
can it not be a good option?
between one’s server and user outside of one’s network.
REPLY ON YOUTUBE
QNAP has significant blame in this latest attack. First, it was their operating system that was hacked (no one had to download a corrupt file). Second, they have all their users emails and all they needed to do is send out notifications to us users alerting us to all the attacks this past year not to mention warning us all to “unplug” immediately when this last attack started. Instead, they remain silent by email even to this day. The only reason I figured out I was hacked is after a month of not logging onto my NAS I found all my files encrypted when I went to grab some photos for my wife. I had to figure out for myself (with the help of bleepingcomputer forum) what was going on, how to get the ransom message back because they had quarantined it. No I didnt have a backup and I guess that is my fault for not understanding the hardware and risks better but I bought the NAS because it was supposed to “simple, safe and secure”. I only use my NAS on my LAN and I’ve never downloaded outside files to it but am not savvy enough to not have it connected to the internet thru my router. If Im lucky enough to get my data back after taking out a loan on my credit card and figuring out this whole Bitcoin thing this weekend, Im done with QNAP and their crappy equipment, buggy software and business approach. QNAP’s silence, irresponsibility and incompetence in dealing with these attacks this past year is the real story here that you all should be talking about as well.
REPLY ON YOUTUBE
What is the most concerning for me as a customer, not that hackers exists, they always did. But that Qnap has backdoor account to my own NAS…… they can remotely access to HBS, force update or whatever….. the clear answer to me to your question is : QNAP is not safe at all, period !
REPLY ON YOUTUBE
I don’t understand why so many “intelligent” people finger-point the victims. Do those guys blame their kids who’s got bullied in school? What a pathetic! NOBODY, NOBODY opened the port to the internet! QNAP got the port opened OUT OF THE BOX! I’m not using mycloud, I didn’t open any port. I didn’t enable auto-update because last year I ever lost files after migrating to the latest build!
This is not the first time they messed up everything. As always, QNAP is trying to escape from their own responsibilities. They pretends nothing happened. Custom service is non-existent. Users forum is full of everything but anything helps fix the issue.
Stay away from QNAP like a plague!
REPLY ON YOUTUBE
Infected last month, huge damages to us, and i guess it’s their ex-engneers who made ransom, and i am sure this company will fall.
REPLY ON YOUTUBE
I use my QNAP for Plex, and I share my Plex with two other friends. This is my second ransomware attack (thank goodness I had backups), so should I stop sharing? Can I make my QNAP secure and still share?
REPLY ON YOUTUBE
Thank you for making this enlightening video! I have now checked and switched off UPnP at my router. I was also watching your Plex setup video where you talk about setting remote access for Plex on a Synology NAS (with DSM 7) . How risky is setting up remote access for Plex to access my media remotely and are there ways to mitigate the risk?
REPLY ON YOUTUBE
I have found QNAP TVS-951X about 350£ (450$) used with 30 days free return + 6TB WD RED drives + 32GB RAM, should I buy it ?? it does look in a fair condition I want to use it for 4k streaming + 1080 and some backup + two or three members of my family watching 1080 content with me also to back up my stuff on it, should I buy it ??
thank you
REPLY ON YOUTUBE
Robbie and Eddie, Thank you for this in depth discussion, and guidance. I’m new to this, bought my nas at the end of November, and have been following a steep learning curve since then. I especially liked the advise to NOT TOUCH your network or nas settings if you do not understand the actions and results. I have to remind myself of that each time I mess with the settings, and have to reconstitute my nas.
REPLY ON YOUTUBE
I bought a single, large (16TB) HDD in recent weeks, plugged that into a free bay in my NAS, created a new storage pool & volume, and copied all my existing NAS Data onto it, and when complete, I pulled that Harddrive out. This is my ‘emergency’ back up, should the worst happen.
REPLY ON YOUTUBE
The Bank & Bank card analogy is a good one.
REPLY ON YOUTUBE
I don’t have remote access to either my QNAP or my Synology directly or through their respective relay systems. Instead, I use OneDrive (OD) as a relay point. My NAS is setup to sync with my OD account. When I’m on the road, my laptop syncs files with OD. So, when I edit a file on my laptop, it then syncs to OD which in turn syncs to my NAS. This won’t work for everyone but it can be a very effective way to effectively gain access to your NAS while working remotely. I don’t do this with the entire NAS, just the folders / files that I may need remotely.
REPLY ON YOUTUBE
Just bought a qnap nas yesterday. Really useful conversation. I have to admit i’m a little more concerned after watching this video than i was before.
REPLY ON YOUTUBE
Probably a recommended setting for beginners users from QNAP might works.
REPLY ON YOUTUBE
We are preparing a new video about how to secure your NAS and your local network.
You can send your external IP address to us via NAScompares.com contact form and we will run free vulnerability tests for you.
This will allow you to identify your network vulnerabilities and open ports etc.
REPLY ON YOUTUBE
Thanks again, last year after qlocker Eddie was adamant that myQnapCloud was safe and I believe the issue was upnp allowing access a hard coded back door.
Do you both still feel myQnapCloud is safe ?
REPLY ON YOUTUBE
Really enjoyed this especially since they got me too. Thank you. Small piece of feedback – it’d be great if you gave Edward a bit more of a chance to speak at times. There are sections where it seems he’s just on the receiving end of a long lecture, as opposed to part of the conversation.
REPLY ON YOUTUBE
Rip out the DOM n install unraid on it 😀
REPLY ON YOUTUBE
Thanks Robert. Thanks Edward.
REPLY ON YOUTUBE
Could you do a video on how to secure your nas? Things like what port to put things on. Stuff like that?
REPLY ON YOUTUBE
im using a tricky way to remotely access my NAS files, by hiding them behind a nextcloud single user on a Pi thats not visible. not infallible, but takes breaking that, just to see files, not alter them or upgrade. if i have to upload, i have to remote into a computer and use other methods. rarely do i need to access files , but it can be done if i have to.
REPLY ON YOUTUBE
After using QNAP NAS devices for years – we’ve lost all confidence in the brand and it’s no longer on our supplier list.
REPLY ON YOUTUBE
TL:DW; version – its a security/ease of use trade-off. If you lock things down users find it too hard to use the features the vendor offers and berates them for it. If you open things up you give users the chance to shoot themselves in the foot, and some will.
Case in point being IoT “plug and play” devices. I was struggling to identify a device on my network today and discovered it had a password-protected web server – I guessed the password on the third attempt. You’d have thought vendors would have learned by now but clearly not.
Another interesting point given the mention of TrueNAS – Unraid ships with all security turned off by default. I think they’ve now realised they erred in doing that, but don’t seem to be in any hurry to fix it. I’ll be keeping any NAS behind a VPN. Wish I could do the same thing with Plex but it seems to need an opening to work properly, so I’ll have to isolate it on a VLAN.
REPLY ON YOUTUBE
One of the mistakes that QNAP made on this was that they actually identified and problem and issued a fix before the attack. But they didn’t make the update mandatory (they can override the user desire on when to take an upgrade). Users that had manually done the upgrade like myself or ones that didn’t have their NAS exposed to the Internet were fine. But other users were hijacked.
REPLY ON YOUTUBE
I did enjoy the video. I got a month ago a TVS-H1288X. We wouldn’t be talking about this if everyone had updated their NAS. QNAP needs to have a shout mode that you can’t miss if the patch fixes a vulnerability. The lack of organized information as not only to what to do but why? Example Port 443. It is recommended to change it but what range and why change it. I assume port scanners don’t deviate from assigned ports and look for low honing fruit. So by changing to 478 it is put out of the scanner range? If we do a router port forwarding to use QBelt on the NAS is that a direct open door to get into the NAS? I am guessing no otherwise why do assigned ports exist. At moment because of questions I have port forwarding off therefore I can’t use QBelt VPN which we are told it safe. My point is there needs to be a source that explains all of this that we can read. I am an engineer and programmer. First thing I did was set up QBelt to my android phone. UPnP was off from beginning. I have turned off myQnapCloud as I am unsure of where it stands safety wise. Has it been broken before? I even bought a certificate from Qnap and installed it. I think you should step in detail on each part of these security setting. What to change? Why you do it. And where to get more if on it. Love your videos
REPLY ON YOUTUBE
Data (physical or electronic) is arguably the most important thing you own the protection of it it more important than money.
If I loose a $50 note it can be replaced with any other $50 note the thing that makes it unique, the little string of numbers in the corner or any stains or creases are not what gives this value to you.
Conversely if you loose 50mb of data it can’t be replaced with any old 50mb of data as it’s uniqueness IS where the value was held. It is by definition irreplaceable/ priceless.
When average joe numpty buys an external HDD, NAS OR starts doing some form of online cloud storage or backup they have stumbled into the realisation that data holds value.
Often it’s a result of learning the hard way and loosing something.
NAS brands really should be held to account for some things but like you say not all.
From a consumer protection point of view, is it fit for purpose? Does it do everything it was advertised to do? Was it free of defects?
I buy a NAS, follow their instructions for setup while using the drives they recommend.
My expectations are:
– My data will be stored there without risk
– My data will be available using ALL advertised methods without putting it at risk
– I will be prevented from accidentally impacting the above two things.
During the setup process there should be a “most users” option that walks you through a VERY simple wizard (most users are not as smart as they think they are… see Dunning-Kruger effect).
Lock out or at least require a certain level of knowledge to unlock the most advanced features. Maybe a big warning when you select advanced option a big simple warning saying “by clicking this we no longer warrant the safety and security of your data” The stuff a car owner should touch is yellow under the bonnet of most cars now. Oil, wiper fluid, etc…
Also as joe numpty does not understand the difference between redundancy, backup etc etc. prompting them to locally encrypt and purchase a offsite data storage plan, backup to another offsite NAS or set up automatic email reminders for periodic backups.
Updates should always come with a have 3 options:
1. Update instantly on release. Early adopters on the bleeding edge (called that for a reason) “the is an update available and will be installed in x hours unless you hit cancel”
2. Delayed update (default most users). There is a new update available it’s currently being installed on some systems. This update will be automatically installed on this hardware after 30 consecutive days of bug free operation globally”. In this mode critical exploit patches are able to be forced if it impacts the last auto update.
3. Auto update off. Notifications on.
I think it’s absolutely NUTS that people give any nas company any form of slack for not treating your data at least as valuable as a bank treats your money. DONT share your pin, unusual behaviour lockdowns of accounts, etc.
Hard to type all this crap on a mobile phone.
REPLY ON YOUTUBE
Great Discussion! Driver’s license…????????????
REPLY ON YOUTUBE
Absolutely, I bought it for the hardware. Not always as inexpensive as I’d like — TS-873A vs 873-AU come to mind.
Is QNAP safe? Well, when it’s a NAS not an iNAS … mostly. I mean, there’s an IOT vector, but this is an IOT issue — does QNAP need to make its NAS safe against a determined in-network hacker? The IOT threat is just a whole nother topic….
The problem is that they market their internet-connectivity, and they need to stop doing that until they get their house in order, because they don’t have their house in order. Their responsiveness to CVEs has been lackluster at best, bordering on dangerously irresponsible. Security concerns are not as front-and-center as they should be. And magic, hard-coded backdoors in software is so gigantically awful — that stuff never should have been checked in to anything that ships to a customer. Astonishingly terrible.
REPLY ON YOUTUBE
Good discussion! But their privacy policy is what drove me away!
REPLY ON YOUTUBE
Great discussion. I like how you alluded to the “everyday man.” The reason I gravitated from Synology to QNAP was #1) Hardware comparison but most importantly #2) Capability to do more thanks to the software’s ability to have a lot less guardrails allowing me to do more.
I am by no means an IT expert, but I want the most hardware for my money and the software capabilities to do it. I also learned early on YOU HAVE to absolutely!!! know what you are getting yourself into before opening up your network with any NAS.
REPLY ON YOUTUBE
There is only one important rule. Never expose your NAS to the internet…until you know exactly what you are doing! Anyway, and always remember, a NAS is NO backup (RAID is not enough backup, either)!
REPLY ON YOUTUBE
Probably time for everyone to realize that these boxes are not good enough for external access. I have 3 qnap boxes and would never expose them to the outside. You want to go outside, go with the big boys like Azure. Qnap is not up for the job. It is fine for your LAN and leave it there.
REPLY ON YOUTUBE
As regarding the backup, one of the reason’s I am looking at buying a NAS is to allow me to put one in my home and one in my parents home, and allow us to both sync our data to have an off site backup.
But this means both need to be exposed on the internet to allow the sync. In this case it I think it makes sense to have both of these to be using the same platform as this includes software to sync.
However if I chose QNAP it is the process of wanting to get the backup capabilities that is exposing me to the data risk.
I am a software developer, (i.e. the worst person in this case since I know enough to be dangerous), but am no ‘Locksmith’, so would really welcome better hand holding and explanation of what the various features are actually doing behing the scenes and what the risks are.
REPLY ON YOUTUBE
QNAP need to open and honest about what vulnerabilities in what software exist on all of their models. If you fix the vulnerabilities sooner via auto-update (and not all vulnerabilities need reboots) then they wouldn’t be in this situation.
REPLY ON YOUTUBE
How about a step by step guide to secure your qnap nas?
REPLY ON YOUTUBE
No, absolutely, NO
REPLY ON YOUTUBE
Safe to save garbage files I guess.
REPLY ON YOUTUBE
This has just happened to me ???? deadbolt… help
REPLY ON YOUTUBE
Another reason to not enable internet access to your NAS.
REPLY ON YOUTUBE
Rob,
Qnap have several must do’s in light of this Dead Bolt ransomware attack with many branching links. Would you be able to do a video in how to do all these security things please?
REPLY ON YOUTUBE
i really hope qnap will do something about those stuff, lately has been quite a lot, anyway, i do love their nas; and if people use it in the proper way, updating the firmwares and all this, everything should be fine in the end
REPLY ON YOUTUBE
This is why god made firewalls and the advice to not expose your NAS to the internet…
REPLY ON YOUTUBE
Question: I’m planning on upgrading from my WD Cloud to a QNAP 453be in the next few days but it will NOT be online. Ever. If it can be avoided. That being said, when I am setting it up for the first time does it “force” me to update the OS or any of the software? Or, can I just set it up completely offline? (I would rather not connect it to the internet specifically for the purpose of never getting any of these bloody attacks. It will be used as a backup device for my family’s laptops and a Plex server for movies we already have on the WD Cloud device (not online).
REPLY ON YOUTUBE
Even though I have Synology (which doesn’t prevent the same from happening), I recommend having an offline backup that is PHYSICALLY unplugged from your NAS After each backup. Even with an offline backup, if it is ejected but not disconnected, all someone has to do is restart the NAS to reconnect and then Infect that backup. You can even take this a step further by initiating backup via USB 3.0 and then disconnecting The router’s internet connection while backing up for peace of mind
then once back up is completed safely eject then physically disconnect offline backup before reconnecting to the internet.
REPLY ON YOUTUBE
2 form authentication helps ?
REPLY ON YOUTUBE
Well bummer, after researching I was on thinking of getting a Qnap instead of a Synology. Now I’m thinking I should get a Synology now.
REPLY ON YOUTUBE
Here we go again. Sigh!
REPLY ON YOUTUBE
I couldn’t even imagine how much those new Gen5 nvme drives are going to cost ????????????????
REPLY ON YOUTUBE
Sea gate drives for the series x are screaming hot. Even when console is off.
REPLY ON YOUTUBE
I have seen a few videos on QNAP re ransomware. Is it more susceptible than synology?
REPLY ON YOUTUBE
04:48 – This video was recorded at 27/01 15:00 GMT. Further information and updates have occurred on this and I have added them at this time marker (regarding forced updates to NAS systems and updates on significantly increased infected systems). If the video looks blurry/360p, then give YouTube 15mins to process or the 720p and 1080p versions (takes them a little time). Cheers for watching.
REPLY ON YOUTUBE